Answer: These errors can be caused by any combination of the following three factors:
Answer: It’s the same problem as noted in the previous topic, but this is the new “improved” security warning screen in Microsoft Internet Explorer. Whereas before IE5.x and IE6.x presented a pop-up that listed the reasons why the certificate is not trusted, IE simply returns a generic error page which recommends that the user close the page. The user is not presented with a direct ‘Yes’ option to proceed, and instead has to click on the embedded Continue to this Website (not recommended) link. For these reasons, it is strongly recommended that all SRA appliances, going forward, have a trusted digital certificate installed.
Answer: Much like the errors shown above for Internet Explorer, Firefox has a unique error message when any certificate problem is detected. The conditions for this error are the same as for the above Internet Explorer errors.
To get past this screen, click the Or you can add an exception link at the bottom, then click the Add Exception button that appears. In the Add Security Exception window that opens, click the Get Certificate button, ensure that Permanently store this exception is checked, and finally, click the Confirm Security Exception button. See below:
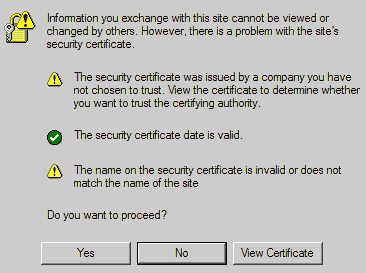
Answer: See the previous section. This occurs when the certificate is not trusted by the Web browser, or the site name requested by the browser does not match the name embedded in the site certificate presented by the SRA appliance during the SSL handshake process. This error can be safely ignored.
Answer: Although the level of encryption is not compromised, users accepting an untrusted certificate introduces the risk of Man-in-the-Middle attacks. Dell SonicWALL recommends installing only trusted certificates or installing the default self-signed certificate in all the clients.
Answer: X509v3.
Answer: Yes.
Answer: Any CA certificate should work if the certificate is in X509v3 format, including Verisign, Thawte, Baltimore, RSA, etc.
Answer: Yes, it does. On the System > Certificates page, do the following:
Answer: We recommend you purchase a multi-year certificate to avoid the hassle of renewing each year (most people forget and when the certificate expires it can create an administrative nightmare). It is also good practice to have all users that will connect to the SRA appliance run Windows Update (also known as Microsoft Update) and install the ‘Root Certificates’ update.
Answer: Yes, but to avoid a browser warning, you will need to install the Microsoft CA’s root certificate into all Web browsers that will connect to the appliance.
Answer: Be sure that you upload a .zip file containing the PEM formatted private key file named "server.key" and the PEM formatted certificate file named "server.crt". The .zip file must have a flat file structure (no directories) and contain only "server.key" and "server.crt" files. The key and the certificate must also match, otherwise the import will fail.
Answer: Click the ‘configure’ icon next to the new certificate and enter the password you specified when creating the Certificate Signing Request (CSR) to finalize the import of the certificate. Once this is done, you can successfully activate the certificate on the SRA appliance.
Answer: It is possible to select a certificate for each Portal under the Portals > Portals: Edit Portal - Virtual Host tab. The portal Virtual Host Settings fields allow you to specify separate IP address, and certificate per portal. If the administrator has configured multiple portals, it is possible to associate a different certificate with each portal. For example, sslvpn.test.sonicwall.com might also be reached by pointing the browser to virtualassist.test.sonicwall.com. Each of those portal names can have its own certificate. This is useful to prevent the browser from displaying a certificate mismatch warning, such as “This server is abc, but the certificate is xyz, are you sure you want to continue?”.
Answer: Select ‘Apache’.
Answer: Yes, the key is exported with the CSR during the CSR generation process. It’s strongly recommended that you can keep this in a safe place with the certificate you receive from the CA. This way, if the SRA appliance ever needs replacement or suffers a failure, you can reload the key and cert. You can also always export your settings from the System > Settings page.
Answer: Yes, client certificates are enforced per Domain or per User on the Users > Local Users: Edit User – Login Policies tab.
Active Directory user name: %ADUSERNAME%
Answer: After a CA certificate has been loaded, the SRA appliance must be rebooted before it is used for client authentication. Failures to validate the client certificate will also cause failures to logon. Among the most common are certificate is not yet valid, certificate has expired, login name does not match common name of the certificate, certificate not sent.