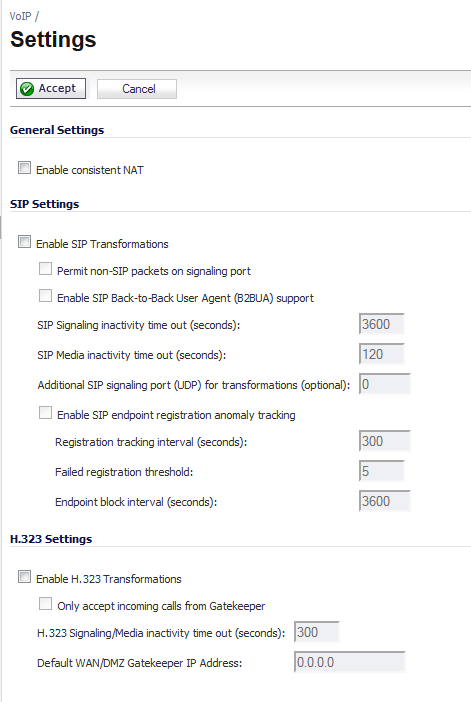
SonicWall <product name> includes the VoIP configuration settings on the VoIP > Settings page. This page is divided into three configuration settings sections: General Settings, SIP Settings, and H.323 Settings.
To enable Consistent NAT, select the Enable Consistent NAT setting and click Accept. This check box is disabled by default.
Selecting Enable SIP Transformations transforms SIP messages between LAN (trusted) and WAN/DMZ (untrusted). You need to check this setting when you want the SonicWall security appliance to do the SIP transformation. If your SIP proxy is located on the public (WAN) side of the SonicWall and SIP clients are on the LAN side, the SIP clients by default embed/use their private IP address in the SIP/Session Definition Protocol (SDP) messages that are sent to the SIP proxy, hence these messages are not changed and the SIP proxy does not know how to get back to the client behind the SonicWall. Selecting Enable SIP Transformations enables the SonicWall to go through each SIP message and change the private IP address and assigned port. Enable SIP Transformations also controls and opens up the RTP/RTCP ports that need to be opened for the SIP session calls to happen. NAT translates Layer 3 addresses but not the Layer 7 SIP/SDP addresses, which is why you need to select Enable SIP Transformations to transform the SIP messages.
|
TIP: In general, you should check the Enable SIP Transformations check box unless there is another NAT traversal solution that requires this feature to be turned off. SIP Transformations works in bi-directional mode, meaning messages are transformed going from LAN to WAN and vice versa.
|
Selecting Permit non-SIP packets on signaling port enables applications such as Apple iChat and MSN Messenger, which use the SIP signaling port for additional proprietary messages. Enabling this check box may open your network to malicious attacks caused by malformed or invalid SIP traffic. This check box is disabled by default.
The Enable SIP Back-to-Back User Agent (B2BUA) support setting should be enabled when the SonicWall security appliance can see both legs of a voice call (for example, when a phone on the LAN calls another phone on the LAN). This setting should only be enabled when the SIP Proxy Server is being used as a B2BUA.
|
TIP: If there is not the possibility of the SonicWall security appliance seeing both legs of voice calls (for example, when calls will only be made to and received from phones on the WAN), the Enable SIP Back-to-Back User Agent (B2BUA) support setting should be disabled to avoid unnecessary CPU usage.
|
SIP Signaling inactivity time out (seconds) and SIP Media inactivity time out (seconds) define the amount of time a call can be idle (no traffic exchanged) before the SonicWall security appliance denying further traffic. A call goes idle when placed on hold. The default time value for SIP Signaling inactivity time out is 1800 seconds (30 minutes). The default time value for SIP Media inactivity time out is 120 seconds (2 minutes).
The Additional SIP signaling port (UDP) for transformations setting allows you to specify a non-standard UDP port used to carry SIP signaling traffic. Normally, SIP signaling traffic is carried on UDP port 5060. However, a number of commercial VOIP services use different ports, such as 1560. Using this setting, the security appliance performs SIP transformation on these non-standard ports.
Select Enable H.323 Transformation in the H.323 Settings section and click Accept to allow stateful H.323 protocol-aware packet content inspection and modification by the SonicWall security appliance. The SonicWall security appliance performs any dynamic IP address and transport port mapping within the H.323 packets, which is necessary for communication between H.323 parties in trusted and untrusted networks/zones. Disable the Enable H.323 Transformation to bypass the H.323 specific processing performed by the SonicWall security appliance.
The H.323 Signaling/Media inactivity time out (seconds) field specifies the amount of time a call can be idle before the SonicWall security appliance denying further traffic. A call goes idle when placed on hold. The default time value for H.323 Signaling/Media inactivity time out is 300 seconds (5 minutes).
The Default WAN/DMZ Gatekeeper IP Address field has a default value of 0.0.0.0. Enter the default H.323 Gatekeeper IP address in this field to allow LAN-based H.323 devices to discover the Gatekeeper using the multicast address 225.0.1.41. If you do not enter an IP address, multicast discovery messages from LAN-based H.323 devices will go through the configured multicast handling.