
IPv6
This appendix provides an overview of SonicWALL’s implementation of IPv6, how IPv6 operates, and how to configure IPv6 for your network. This appendix contains the following sections:
The following sections provide an overview of IPv6:

SonicWALL has met the requirements for "IPv6 Ready" Phase-1 and Phase-2, as specified by the IPv6 Forum, a world-wide consortium providing technical guidance for the deployment of IPv6. The IPv6 Ready Logo Program is a conformance and interoperability testing program intended to increase user confidence by demonstrating that IPv6 is available now and ready to be used.
The IPv6 Ready series of tests extends from a basic level of minimum coverage in Phase-1 to a more complete coverage with Phase-2:
Phase-1 (Silver) Logo: In a first stage, the Logo indicate that the product includes IPv6 mandatory core protocols and can interoperate with other IPv6 implementations.
Phase-2 (Gold) Logo: The "IPv6 ready" step implies a proper care, technical consensus and clear technical references. The IPv6 Ready Logo will indicate that a product has successfully satisfied strong requirements stated by the IPv6 Logo Committee (v6LC).
SonicWALL has been certified for Phase 2 (Gold) IPv6 Ready status. A future Phase-3 level of IPv6 Ready coverage is currently being developed.
For more information, see: http://www.ipv6ready.org/
Every device that is connected to the Internet (computer, printer, smart phone, smart meter, etc.) requires an IP address. The Internet Protocol version 4 (IPv4) provides for approximately 4.3 billion unique IP addresses. The rapid global expansion in usage of the Internet, mobile phones, and VoIP telephony will soon lead to the exhaustion of these 4.3 billion IP addresses.
On February 3rd, 2011, the Internet Assigned Numbers Authority (IANA) distributed the last-remaining blocks of IPv4 addresses to the Regional Internet Registries (RIRs). After the RIRs distribute these addresses to ISPs later this year, the world’s supply of new IPv4 addresses will be exhausted.
Luckily, the Internet Engineering Task Force (IETF) began planning for this day back around 1992, and in 1998, RFC 2460 was published to define Internet Protocol, Version 6 (IPv6). By increasing the address length from 32 bits to 128 bits, IPv6 dramatically increases the number of available addresses compared to IPv4:
IPv4: 4,294,967,296 addresses
IPv6: 340,282,366,920,938,463,463,374,607,431,768,211,456 addresses
Understanding IPv6 Addresses
IPv6 addresses are written in eight groups of four hexadecimal digits separated by colons, in the form:
XXXX:XXXX:XXXX:XXXX:XXXX:XXXX:XXXX:XXXX
IPv6 addresses are logically divided into two parts: a 64-bit (sub-)network prefix, and a 64-bit interface identifier. Here is an example of an IPv6 address:
2001:0db8:85a3:0000:0000:8a2e:0370:7334
Note The hexadecimal digits in IPv6 addresses are case-insensitive.
IPv6 address can be abbreviated using the following two rules:
Leading zeroes within a 16-bit value may be omitted. Thus, our example address can be abbreviated from the full form:
2001:0db8:85a3:0000:0000:8a2e:0370:7334
to this abbreviated form:
2001:db8:85a3:0:0:8a2e:370:7334
Any number of consecutive groups of four zeros (technically 16-bits of zeros) can be expressed by a double colon (the “::” symbol). Combing these two rules, our example address can be abbreviated from the full form:
2001:0db8:85a3:0000:0000:8a2e:0370:7334
to this abbreviated form:
2001:db8:85a3::8a2e:370:7334
|
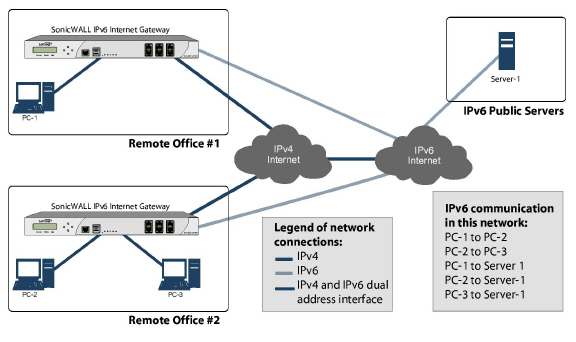
Note Networks must have IPv4 internet connectivity in order to get connected to IPv6 internet.
Note IPv6 stack must be enabled for computers at the local network sites.
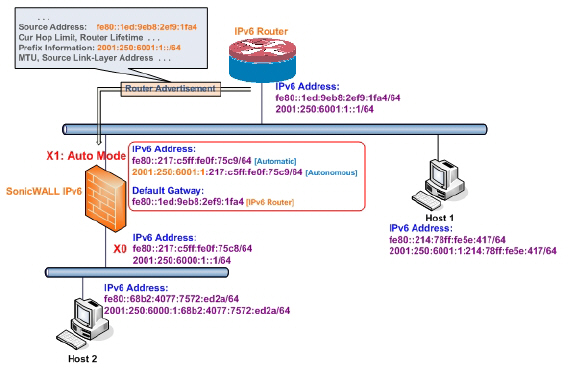
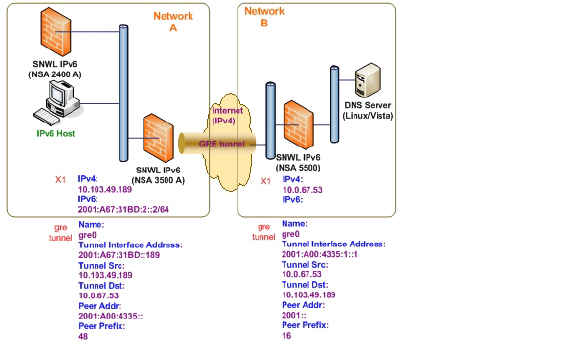
Here is a simplified picture showing connectivity model for a typical IPv6 deployment.
The following diagram shows a comparison of the header elements between IPv4 and IPv6.
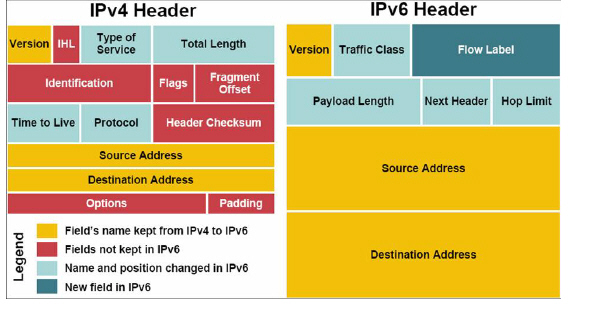
IPv6 brings some key features to improve the limitations exposed by IPv4. The new IP standard extends IPv4 in a number of important aspects:
New, simplified IPv6 header format
Massively large number of available IPv6 addresses
Efficient and hierarchical addressing and routing infrastructure
Auto address assignment to hosts and routers using Neighbor Discovery Protocol (NDP) and DHCPv6
Stateless and stateful address configuration
Built-in security - AH and ESP strongly recommended
Better support for QoS - Flow label in the header
New protocol for neighboring node interaction
Extensibility for new features using extension headers
SonicWALL IPv6 Feature Support
The following is a list of IPv6 services and features that are currently supported by SonicWALL:
6to4 tunnel (allows IPv6 nodes to connect to outside IPv6 services over an IPv4 network)
Access Rules
Address Objects
Attack prevention:
Land Attack
Ping of Death
Smurf
SYN Flood
Connection Cache
Connection Monitor
DHCP
DNS client
DNS lookup and reverse name lookup
EPRT
EPSV
FTP
High Availability:
Connection Cache
FTP
NDP
HTTP/HTTPS management over IPv6
ICMP
IKEv2
IP Spoof Protection
IPv4 Syslog messages, including messages with IPv6 addresses
Layer 2 Bridge Mode
Logging IPv6 events
Login uniqueness
Multicast Routing with Multicast Listener Discovery
NAT
Neighbor Discovery Protocol
NetExtender connections for users with IPv6 addresses
Packet Capture
Ping
Policy Based Routing
Remote management
Site-to-site IPv6 tunnel with IPSec for security
SonicPoint IPv6 support
Security services for IPv6 traffic with DPI
SSL VPN
Stateful inspection of IPv6 traffic
User status
VPN policies
Wireless
SonicWALL IPv6 Features Not Currently Supported
The following is a list of IPv6 services and features that are not currently supported by SonicWALL.
Note SonicOS Enhanced 5.5.6.0 is a dual IP stack firmware. Features that are not supported for IPv6 are still supported for IPv4.
Anti-Spam
Command Line Interface
Connection Limiting for IPv6 connections
DHCP over VPN
DHCP Relay
Dynamic Address Objects for IPv6 addresses
Dynamic DNS
Dynamic Routing (RIP and OSPF)
FQDN
Global VPN Client (GVC)
GMS
H.323
High Availability support for the following features:
Dynamic Address Objects
IPv6 management IP address
Multicast
SonicPoints
VoIP
IKEv1
IPv6 Syslog messages
L2TP
LDAP
MAC-IP Anti-Spoof
NAT load balancing
NAT between IPv6 and IPv4 addresses
NetBIOS over VPN
NTP
Oracle SQL/Net
QoS Mapping
PPPoE
RADIUS
RAS Multicast Forwarding
RTSP
Route-based VPNs
Single Sign On
SIP
SMTP Real-Time Black List (RBL) Filtering
SNMP
SSH
Transparent Mode
ViewPoint
Virtual Assistant
Virtualization
VLAN interfaces with IPv6 addresses
Web proxy
This section lists the IPv6 RFCs that are supported in the SonicOS Enhanced 5.5.6.0 release.
TCP/IP stack and Network Protocols
RFC 1886 DNS Extensions to support IP version 6 [IPAPPL dns client]
RFC 1981 Path MTU Discovery for IPv6
RFC 2113 IP Router Alert Option
RFC 2373 IPv6 Addressing Architecture
RFC 2374 An IPv6 Aggregatable Global Unicast Address Format (obsoleted by 3587)
RFC 2375 IPv6 Multicast Address Assignments
RFC 2460 IPv6 specification
RFC 2461 Neighbour discovery for IPv6
RFC 2462 IPv6 Stateless Address Autoconfiguration
RFC 2463 ICMPv6 for IPv6 specification
RFC 2464 Transmission of IPv6 Packets over Ethernet Networks
RFC 2473 Generic Packet Tunneling in IPv6 Specification
RFC 2474 Definition of the Differentiated Services Field (DS Field) in the IPv4 and IPv6 Headers
RFC 2553 Basic Socket Interface Extensions for IPv6
RFC 2710 Multicast Listener Discovery (MLD) for IPv6
RFC 2711 IPv6 Router Alert Option
RFC 2784 Generic Routing Encapsulation
RFC 2893 Transition Mechanisms for IPv6 Hosts and Routers
RFC 2991 Multipath Issues in Unicast and Multicast Next-Hop Selection
RFC 3056 Connection of IPv6 Domains via IPv4 Clouds
RFC 3484 Default Address Selection for Internet Protocol version 6 (IPv6) (no policy hooks)
RFC 3493 Basic Socket Interface Extensions for IPv6
RFC 3513 Internet Protocol Version 6 (IPv6) Addressing Architecture
RFC 3542 Advanced Sockets Application Program Interface (API) for IPv6
RFC 3587 IPv6 Global Unicast Address Format (obsoletes 2374)
IPsec Conformance
RFC 1826 IP Authentication Header [old AH]
RFC 1827 IP Encapsulating Security Payload (ESP) [old ESP]
NAT Conformance
RFC 2663 IP Network Address Translator (NAT) Terminology and Considerations.
RFC 3022 Traditional IP Network Address Translator (Traditional NAT).
DNS Conformance
RFC 1886 DNS Extensions to support IP version 6
This section lists the IPv6 RFCs that are currently not supported in the SonicOS Enhanced 5.5.6.0 release.
RFC 2002 IP Mobility Support
RFC 2766 Network Address Translation - Protocol Translation (NAT-PT)
RFC 2472 IP Version 6 over PPP
RFC 2452 IP Version 6 Management Information Base for the Transmission Control Protocol.
RFC 2454 IP Version 6 Management Information Base for the User Datagram Protocol.
RFC 2465 Management Information Base for IP Version 6: Textual Conventions and General Group.
The following sections describe how to configure IPv6:
IPv6 interfaces are configured on the Network > Interfaces page by clicking the IPv6 option for the View IP Version radio button at the top right corner of the page.
By default, all IPv6 interfaces appear as routed with no IP address. Multiple IPv6 addresses can be added on the same interface. Auto IP assignment can only be configured on WAN interfaces.
Each interface can be configured to receive router advertisement or not. IPv6 can be enabled or disabled on each interface.
Note The zone assignment for an interface must be configured through the IPv4 interface page before switching to IPv6 mode.
The following sections describe IPv6 interface configuration:
IPv6 Interface Configuration Constraints
The HA interface cannot be configured for IPv6.
Only the parent interface of a SwitchPort group can be configured as an IPv6 interface, hence all children of a switch port group must be excluded from this list.
Zone and Layer 2 Bridge groups are shared configurations between by IPv4 and IPv6 on an interface. Once they are configured on the IPv4 side, the IPv6 side of the interface will use the same configuration.
Default Gateway and DNS Servers can only be configured for WAN zone interfaces.
VLAN interfaces are not currently supported.
Configuring an Interface for IPv6 Static Mode
Static mode provides user a way to assign static IPv6 address as opposed to an auto-assigned address. Using static mode, the IPv6 interface can still listen for Router Advertisements and learn an autonomous address from the appropriate prefix option. Static Mode does not disturb the running of Stateless Address Autoconfiguration on IPv6 interface unless the user manually disables it.
The following diagram shows a sample topology with IPv6 configured in static mode.
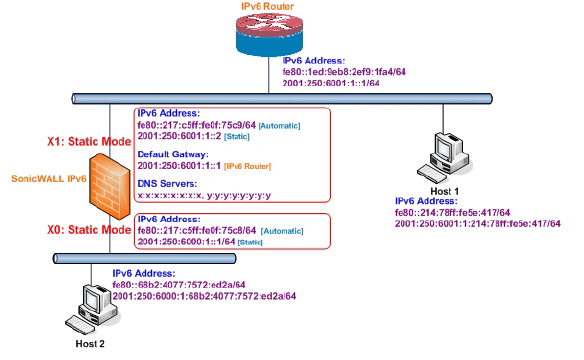
3 types of IPv6 address are possible to assign under this mode:
Automatic Address
Autonomous Address
Static Address
To configure an interface for a static IPv6 address, perform the following steps:
Navigate to the Network > Interfaces page.
Click on the IPv6 button at the top right corner of the page. IPv6 addresses for the appliance are displayed.
Click on the Configure icon for the interface you want to configure an IPv6 address for. The Edit Interface window displays.
Note The zone assignment for interfaces must be configured on the IPv4 addressing page. To modify the zone assignment for an IPv6 interface, click the IPv4 button at the top right of the page, modify the zone for the interface, and then return to the IPv6 interface page.
In the IP Assignment pulldown menu, select Static.
Enter the IPv6 Address for the interface.
Enter the Prefix Length for the address.
If this is the primary WAN interface, enter the IPv6 address of the Default Gateway. If this is not the primary WAN interface, any Default Gateway entry will be ignored, so you can leave this as ::. (The double colon is the abbreviation for an empty address, or 0:0:0:0:0:0:0:0.)
If this is the primary WAN interface, enter up to three DNS Server IPv6 addresses. Again, if this is not the primary WAN interface, any DNS Server entries will be ignored.
Select Enable Router Advertisement to make this an advertising interface that distributes network and prefix information.
Select Advertise Subnet Prefix of IPv6 Primary Static Address to add a default prefix into the interface advertising prefix list. This prefix is the subnet prefix of interface IPv6 primary static address. This option will help all hosts on the link stay in the same subnet.
Configuring Advanced IPv6 Interface Options and Multiple IPv6 Addresses
Perform the following steps to modify Advanced IPv6 interface options or to configure multiple static IPv6 addresses.
In the Edit Interface window, click on the Advanced tab.
Click the Add Address button to configure multiple static IPv6 addresses for the interface.
Note Multiple IPv6 addresses can only be added for an interface that is configured for Static IPv6 address mode. Multiple IPv6 addresses cannot be configured for Auto or DHCPv6 modes.
Enter the IPv6 Address for the additional address for the interface.
Enter the Prefix Length for the address.
Select Advertise Subnet Prefix of IPv6 Primary Static Address to add a default prefix into the interface advertising prefix list. This prefix is the subnet prefix of interface IPv6 primary static address. This option will help all hosts on the link stay in the same subnet.
Click OK.
The following additional options can be configured on the Advanced tab under the Advanced Settings heading:
Select Disable all IPv6 Traffic on the Interface to stop the interface from handling all IPv6 traffic. Disabling IPv6 traffic can improve firewall performance for non-IPv6 traffic. If the firewall is deployed in a pure IPv4 environment, SonicWALL recommends enabling this option.
Select Enable Listening to Router Advertisement to have the firewall receive router advertisement. If disabled, the interface filters all incoming Router Advertisement message, which can enhance security by eliminating the possibility of receiving malicious network parameters (e.g. prefix information or default gateway). This option is not visible for Auto mode. In Auto mode, it is always enabled.
Select Enable Stateless Address Autoconfiguration to allow autonomous IPv6 addresses to be assigned to this interface. If unchecked, all assigned autonomous IPv6 address will be removed from this interface. This option is not visible for Auto mode. In Auto mode, it is always enabled.
Enter a numeric value for Duplicate Address Detection Transmits to specify the number of consecutive Neighbor Solicitation messages sent while performing Duplicate Address Detection (DAD) before assigning a tentative address to interface. A value of 0 indicates that DAD is not performed on the interface.
Similar with IPv4 gratuitous ARP, IPv6 node uses Neighbor Solicitation message to detect duplicate IPv6 address on the same link. DAD must be performed on any Unicast address (except Anycast address) before assigning a tentative to an IPv6 interface.
Configuring Router Advertisement Settings
Router Advertisement allows IPv6 routers to advertise DNS recursive server addresses to IPv6 hosts. Router Advertisement-based DNS configuration is a useful, optional alternative in networks where an IPv6 host's address is autoconfigured through IPv6 stateless address autoconfiguration, and where the delays in acquiring server addresses and communicating with the servers are critical. Router Advertisement allows the host to acquire the nearest server addresses on every link. Furthermore, it learns these addresses from the same RA message that provides configuration information for the link, thereby avoiding an additional protocol run. This can be beneficial in some mobile environments, such as with Mobile IPv6. SonicWALL’s implementation of IPv6 is full conformable with RFC 4861 in Router and Prefix Discovery.
Note Router Advertisement can only be enabled when interface is under Static mode.
To configure Router Advertisement for an IPv6 interface, perform the following steps.
In the Edit Interface window, click on the Router Advertisement tab.
Select the Enable Router Advertisement checkbox to have make this an advertising interface that will distribute network and prefix information.
Optionally, you can modify the following Router Advertisement settings:
Router Adv Interval Range - The time interval allowed between sending unsolicited multicast Router Advertisements from the interface, in seconds.
Link MTU - The recommended MTU for the interface link. A value of 0 means firewall will not advertise link MTU for the link.
Reachable Time - The time that a node assumes a neighbor is reachable after having received a reachability confirmation. A value of 0 means this parameter is unspecified by this firewall.
Retrans Time - The time between retransmitted Neighbor Solicitation messages. A value of 0 means this parameter is unspecified by this firewall.
Current Hop Limit - The default value that should be placed in the Hop Count field of the IP header for outgoing IP packets. A value of 0 means this parameter is unspecified by this firewall.
Router Lifetime - The lifetime when firewall is accepted as a default router. A value of 0 means that the router is not a default router.
Select the Managed checkbox to set the managed address configuration flag in the Router Advertisement message. If set, it indicates that IPv6 addresses are available via Dynamic Host Configuration Protocol.
Select the Other Configuration checkbox to set the Other configuration flag in Router Advertisement message. If set, it indicates that other configuration information is available via Dynamic Host Configuration Protocol.
Configuring Router Advertisement Prefix Settings
Click the Add Prefix button to configure an advertising prefix. Advertising prefixes are used for providing hosts with prefixes for on-link determination and Address Autoconfiguration.
Enter the Prefix that is to be advertised with the Router Advertisement message.
Enter the Valid Lifetime to set the length of time (in minutes) that the prefix is valid for the purpose of on-link determination. A value of “71582789” means the lifetime is infinite.
Enter the Preferred Lifetime to set the length of time that addresses generated from the prefix via stateless address autoconfiguration remain preferred. A value of “71582789” means the lifetime is infinite.
Optionally click the On-link checkbox to enable the on-link flag in Prefix Information option, which indicates that this prefix can be used for on-link determination.
Optionally click the Autonomous checkbox to enable the autonomous address-configuration flag in Prefix Information option, which indicates that this prefix can be used for stateless address configuration.
Click OK.
Configuring an Interface for DHCPv6 Mode
DHCPv6 (DHCP for IPv6) is a client/server protocol that provides stateful address configuration or stateless configuration setting for IPv6 hosts. DHCPv6 client is enabled to learn IPv6 address and network parameters when interface is configured to DHCPv6 mode.
DHCPv6 defines two different configuration modes:
DHCPv6 stateful mode: DHCPv6 clients require IPv6 address together with other network parameters (e.g. DNS Server, Domain Name, etc.).
DHCPv6 stateless mode: DHCPv6 client only obtains network parameters other than IPv6 address. Choosing which kind of those modes depends on Managed (M) Address Configuration and Other (O) Configuration flag in the advertised Router Advertisement message:
M = 0, O = 0: No DHCPv6 infrastructure.
M = 1, O = 1: IPv6 host use DHCPv6 for both IPv6 address and other network parameter settings.
M = 0, O = 1: IPv6 host use DHCPv6 only for IPv6 address assignment.
M = 1, O = 0: IPv6 host use DHCPv6 only for other network parameter settings, which known as DHCPv6 stateless.
The following diagram shows a sample DHCPv6 topology.
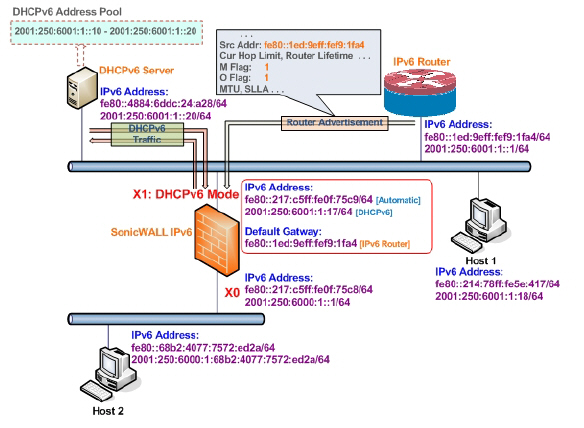
There are three types of IPv6 addresses that can be assign under DHCPv6:
Automatic Address
Autonomous Address
IPv6 Address assigned through DHCPv6 client
To configure an interface for a DHCPv6 address, perform the following steps:
Navigate to the Network > Interfaces page.
Click on the IPv6 button at the top right corner of the page. IPv6 addresses for the appliance are displayed.
Click on the Configure icon for the interface you want to configure an IPv6 address for. The Edit Interface window displays.
In the IP Assignment pulldown menu, select DHCPv6.
The following options can be configured for IPv6 interfaces configured for DHCPv6 mode:
Use Rapid Commit Option - If enabled, DHCPv6 client use Rapid Commit Option to use the two message exchange for address assignment.
Send hints for renewing previous IP on startup - If enabled, DHCPv6 client will try to renew the address assigned before when firewall startup.
Set the DHCPv6 Mode for the interface. As required by RFC, DHCPv6 client depends on Router Advertisement message to decide which mode (stateful or stateless) it should choose. This definition will limit user's choice if they want to determine DHCPv6 mode by itself. SonicWALL’s implementation of DHCPv6 defines two different modes to balance the conformance and flexibility:
Automatic - In this mode, IPv6 interface configures IPv6 addresses using stateless/stateful autoconfiguration in accord with the M and O settings in the most recently received router advertisement message.
Manual - In Manual mode, DHCPv6 mode is manually configured regardless of any received Router Advertisement. The Only Request Stateless Information option will determine which DHCPv6 mode is used. If this option is unchecked, DHCPv6 client is under stateful mode; if it is checked, DHCPv6 client is under stateless mode and only obtains network parameters.
Optionally, select the Only Request Stateless Information checkbox to have DHCPv6 clients only requests network parameter setting from the DHCPv6 server. The IPv6 address is assigned through stateless auto-configuration.
Click OK to complete the configuration, or click the Advanced tab to configure Advanced options or click the Protocol tab to view DHCPv6 stateful and stateless configuration information.
Configuring Advanced Settings for an IPv6 Interface
The following options can be configured on the Advanced tab of the IPv6 Edit Interface window:
Select Disable all IPv6 Traffic on the Interface to stop the interface from handling all IPv6 traffic. Disabling IPv6 traffic can improve firewall performance for non-IPv6 traffic. If the firewall is deployed in a pure IPv4 environment, SonicWALL recommends enabling this option.
Select Enable Listening to Router Advertisement to have the firewall receive router advertisement. If disabled, the interface filters all incoming Router Advertisement message, which can enhance security by eliminating the possibility of receiving malicious network parameters (e.g. prefix information or default gateway). This option is not visible for Auto mode. In Auto mode, it is always enabled.
Select Enable Stateless Address Autoconfiguration to allow autonomous IPv6 addresses to be assigned to this interface. If unchecked, all assigned autonomous IPv6 address will be removed from this interface. This option is not visible for Auto mode. In Auto mode, it is always enabled.
Enter a numeric value for Duplicate Address Detection Transmits to specify the number of consecutive Neighbor Solicitation messages sent while performing Duplicate Address Detection (DAD) before assigning a tentative address to interface. A value of 0 indicates that DAD is not performed on the interface.
Similar with IPv4 gratuitous ARP, IPv6 node uses Neighbor Solicitation message to detect duplicate IPv6 address on the same link. DAD must be performed on any Unicast address (except Anycast address) before assigning a tentative to an IPv6 interface.
DHCPv6 Protocol Tab
When configuring an IPv6 interface in DHCpv6 mode, the Protocol tab displays additional DHCPv6 information.
The following information is displayed on the Protocol tab:
DHCPv6 State: If the interface is configured for Stateless mode, the DHCPv6 State will be Stateless. If the interface is configured for Stateful mode, the DHCPv6 State will be either Enable or Disabled. When the interface is in Stateful, DHCPv6 mode, mousing over the icon to the left of the DHCPv6 State will display current Router Advertisement information for the interface.
DHCPv6 Server: The IPv6 address of the DHCPv6 server.
Stateful Addresses Acquired via DHCPv6: Displays information on any acquired stateful IPv6 addresses.
DNS Servers: The IPv6 addresses of any DNS Servers.
Configuring an Interface for Auto Mode
Auto mode utilities IPv6’s Stateless Address Autoconfiguration to assign IPv6 address. This mode does not require any manual address configuration by the network administrator. The firewall listens to the network and receives prefix information from neighboring routers. The IPv6 Stateless Address Autoconfiguration feature performs all configuration details, such as IPv6 address assignment, address deleting for address conflicting or lifetime expiration, and default gateway selection based on the information collected from on-link router.
Note Auto mode can only be configured for the WAN zone. For security consideration, Auto mode is not available on LAN zone interface.
The following diagram shows a sample topology for IPv6 configured in Auto mode.
In this mode, 2 types of IPv6 address are possible to assign:
Automatic Address - The interface default link-local address. It is never timed out and is not able to be edited or deleted.
Autonomous Address - Assigned from Stateless Address Autoconfiguration. Users can manually delete the address if they do not want to wait for its valid lifetime expires.
To configure an IPv6 interface for Auto mode, perform the following tasks:
Navigate to the Network > Interfaces page.
Click on the IPv6 button at the top right corner of the page. IPv6 addresses for the appliance are displayed.
Click on the Configure icon for the interface you want to configure an IPv6 address for. The Edit Interface window displays.
In the IP Assignment pulldown menu, select Auto.
Optionally, you can select enter a numeric value for Duplicate Address Detection Transmits on the Advanced tab to specify the number of consecutive Neighbor Solicitation messages sent while performing Duplicate Address Detection (DAD) before assigning a tentative address to interface. A value of 0 indicates that DAD is not performed on the interface.
Click OK.
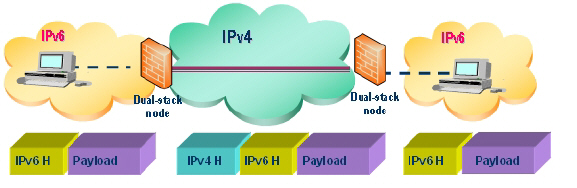
Configuring IPv6 Tunnel Interfaces
This section describes how to tunnel IPv4 packets through IPv6 networks and IPv6 packets through IPv4 networks. For instance, in order to pass IPv6 packets through the IPv4 network, the IPv6 packet will be encapsulated into an IPv4 packet at the ingress side of a tunnel. When the encapsulated packet arrives at the egress of the tunnel, the IPv4 packet will be de-capsulated.
Tunnels can be either automatic or manually configured. A configured tunnel determines the endpoint addresses by configuration information on the encapsulating node. An automatic tunnel determines the IPv4 endpoints from the address of the embedded IPv6 datagram. IPv4 multicast tunneling determines the endpoints through Neighbor Discovery.
The following diagram depicts an IPv6 to IPv4 tunnel.
The following sections describe IPv6 Tunnel Interface configuration:
Configuring the 6to4 Auto Tunnel
The 6to4 Auto Tunnel is an automatic tunnel: tunnel endpoints are extracted from the encapsulated IPv6 datagram. No manual configuration is necessary.
6to4 tunnels use a prefix of the form “2002:tunnel-IPv4-address::/48” to tunnel IPv6 traffic over IPv4. (for example, if the tunnel’s IPv4 endpoint has the address a01:203, the 6to4 tunnel prefix is “2002:a01:203::1.”) Routers advertise a prefix of the form “2002:[IPv4]:xxxx/64” to IPv6 clients. For complete information, see RFC 3056.
The following diagram shows a sample 6to4 auto tunnel topology.
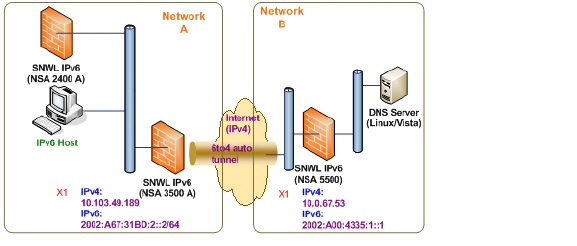
In the example, customers do not need to specify the tunnel endpoint, but only need to enable the 6to4 auto tunnel. All packets with a 2002 prefix will be routed to the tunnel, and the tunnel's IPv4 destination will be extract from the destination IPv6 address.
6to4 tunnels are easy to configure and use. Users must have a global IPv4 address and IPv6 address, which must also have a 2002 prefix. Therefore, in general, user can only access network resource with a 2002 prefix.
Note Only one 6to4 auto tunnel can be configured on the firewall.
To configure the 6to4 tunnel on the firewall, perform the following steps:
Navigate to the Network > Interfaces page.
Click the Add Interface button.
Select the Zone for the 6to4 tunnel interface. This is typically the WAN interface.
In the Tunnel Type pulldown menu, select 6to4 Auto Tunnel Interface.
By default, the interface Name is set to 6to4AutoTun.
Select the Enable IPv6 6to4 Tunnel checkbox.
Optionally, you can configure Management login or User Login over the 6to4 tunnel.
Click OK.
Configuring 6to4 Relay for Non-2002 Prefix Access
By default, 6to4 auto tunnel can only access the destination with a 2002 prefix. The 6to4 relay feature can be used to access non-2002 prefix destinations. To enable 6to4 relay, simply create a Route Policy to route all traffic destined for 2003 prefixes over the 6to4 auto tunnel interface, as shown in the following example.
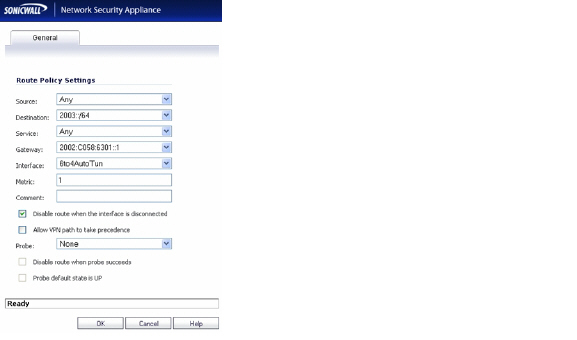
This static route can be added on the 6to4 auto tunnel interface to enable the relay feature, which makes it possible to access the IPv6 destination with non-2002: prefix through 6to4 tunnel. Note that, the gateway must be the IPv6 address with the 2002: prefix.
Configuring a Manual Ipv6 Tunnel
To configure the 6to4 tunnel on the firewall, perform the following steps:
Navigate to the Network > Interfaces page.
Click the Add Interface button.
Select the Zone for the tunnel interface.
In the Tunnel Type pulldown menu, select IPv6 Manual Tunnel Interface.
Enter a Name for the tunnel interface.
Enter the Remote IPv4 address for the tunnel endpoint.
For the Remote IPv6 network select an IPv6 Address object, which can be a group, range, network, or Host.
Optionally, you can configure Management login or User Login over the 6to4 tunnel.
Click OK.
GRE can be used to tunnel IPv4 and IPv6 traffic over IPv4 or IPv6. GRE tunnels are static tunnels where both endpoints are specified manually. The following diagram shows a sample GRE IPv6 tunnel.
The configuration of a GRE tunnel is similar to a manual tunnel, except GRE Tunnel Interface is selected for the Tunnel Type.
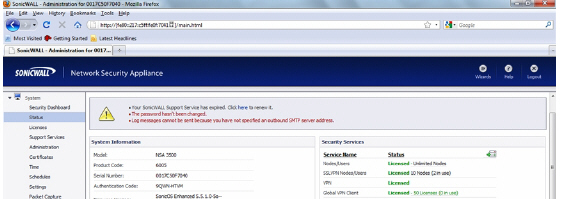
Accessing the SonicWALL User Interface Using IPv6
After IPv6 addressing has been configured on the firewall, the SonicWALL user interface can be accessed by entering the IPv6 of the firewall in your browser’s URL field.
DNS for IPv6 is configured in the same method as for IPv4. Simply click the IPv6 option in the View IP Version radio button at the top left of the Network > DNS page.
IPv6 address objects or address groups can be added in the same manner as IPv4 address objects. On the Network > Address Objects page, the View IP Version radio button has three options: IPv4 only, IPv6 only, or IPv4 and IPv6.
Note Address Objects of type Host, Range and Network are supported. Dynamic address objects for MAC and FQDN are not currently supported for IPv6 hosts.
IPv4 interfaces define a pair of a default Address Object (DAO) and an Address Object Group for each interface. The basic rule for IPv4 DAO is each IPv4 address corresponds to 2 address objects: Interface IP and Interface Subnet. There are also couples of AO groups for Zone Interface IP, Zone Subnets, All Interface IP, All Interface Management IP, etc.
IPv6 interface prepares the same DAO set for each interface. Because multiple IPv6 can be assigned to one interface, all of those address can be added, edited, and deleted dynamically. Therefore, IPv6 DAOs need to be created and deleted dynamically.
To address this, DAOs are not generated dynamically for IPv6 interfaces. Only limited interface DAO are created, which results in limitation support for other module which needs to refer interface DAO.
Policy Based Routing is fully supported for IPv6 by selecting IPv6 address objects and gateways for route policies on the Network > Routing page. On the Network > Routing page, the View IP Version radio button has three options: IPv4 only, IPv6 only, or IPv4 and IPv6.
NAT policies can be configured for IPv6 by selecting IPv6 address objects on the Network > NAT Policies page. On the Network > NAT Policies page, the View IP Version radio button has three options: IPv4 only, IPv6 only, or IPv4 and IPv6.
When configuring IPv6 NAT policies, the source and destination objects can only be IPv6 address objects.
Note IPv6 probing for NAT policies is not currently supported.
The Neighbor Discovery Protocol (NDP) is a new messaging protocol that was created as part of IPv6 to perform a number of the tasks that ICMP and ARP accomplish in IPv4. Just like ARP, Neighbor Discovery builds a cache of dynamic entries, and the administrator can configure static Neighbor Discovery entries. The following table shows the IPv6 neighbor messages and functions that are analogous to the traditional IPv4 neighbor messages.
|
To configure NDP, navigate to the Network > Neighbor Discovery page.
The Static NDP feature allows for static mappings to be created between a Layer 3 IPv6 address and a Layer 2 MAC address. To configure a Static NDP entry, perform the following steps:
On the Network > Neighbor Discovery page, click the Add button.
In the IP Address field, enter the IPv6 address for the remote device.
In the Interface pulldown menu, select the interface on the firewall that will be used for the entry.
In the MAC Address field, enter the MAC address of the remote device.
Click OK. The static NDP entry is added.
The NDP Cache table displays all current IPv6 neighbors. The follow types of neighbors are displayed:
REACHABLE - The neighbor is known to have been reachable within 30 seconds.
STALE - The neighbor is no longer known to be reachable, and traffic has been sent to the neighbor within 1200 seconds.
STATIC - The neighbor was manually configured as a static neighbor.
The Network > Multicast Routing page is used to configure multicast settings for IPv6, which are divided into the two following sections:
Maintaining interoperability between IPv6 and IPv4 networks is one of the main challenges of implementing IPv6 in a network. While packet-based multicast translation can be used, SonicWALL supports a multicast proxy solution that can be deployed at the border between IPv6 and IPv4 networks. The SonicWALL receives multicast data from the IPv4 network, caches it, and then multicasts the data to the IPv6 network. (And vice versa for sending multicast data from the IPv6 to the IPv4 network.) This is accomplished without the need for packet-based translation.
To configure Multicast Proxy between IPv6 and IPv4 networks, perform the following steps:
Navigate to the Network > Multicast Routing page.
Select the Enable Multicast Proxy checkbox.
In the Upstream Interface pulldown menu, select the interface that is connected to the IPv6 network.
In the Downstream Interface pulldown menu, select the interface that is connected to the IPv4 network.
Click the Accept button. Multicast data will now be proxied \.
The Multicast Listener Discovery (MLD) protocol is used by IPv6 routers to discover multicast listeners that are directly connected to the firewall. MLD performs a similar function for IPv6 that IGMP is used for in IPv4. There are two versions of MLD. MLDv1 is similar to IGMPv2, and MLDv2 similar to IGMPv3.
|
MLD functionality does not require any explicit configuration. There are several variables that can be fine-tuned to modify the MLD behavior:
Multicast Router Query Interval: Specifies the length in seconds between MLD queries. The default value is 125 seconds.
Multicast Last Listener Query Interval: The maximum time that the router waits before deleting a nonresponsive port from the multicast group. Reducing this value will reduce the time required for the firewall to detect the departure of the last listener for a multicast address or source. The default value is 1000 milliseconds (1 second).
Multicast Router Query Response Interval: The Maximum Response Delay that is inserted into the periodic MLD queries. By varying the Multicast Router Query Response Interval, an administrator may tune the burstiness of MLD messages on the link; larger values make the traffic less bursty, as host responses are spread out over a larger interval. The Multicast Router Query Response Interval must be less than the Query Interval.The default value is 10000 milliseconds (10 seconds).
Multicast Router Robustness Variable: Specifies the number of queries that will be sent with no response before the target is deleted. This variable allows tuning the protocol according to the expected packet loss on a link. For lossy links (wireless connections, for example), the value of the Robustness Variable may be increased. The default value is 2. The Robustness Variable should not be configured for less than 2.
DHCPv6 server can be configured similar to IPv4 after selecting the IPv6 option in the View IP Version radio button at the top left of the Network > DNS page.
IPv6 Access Rules Configuration
IPv6 firewall access rules can be configured in the same manner as IPv4 access rules by choosing IPv6 address objects instead of IPv4 address objects. On the Firewall > Access Rules page, the View IP Version radio button has three options: IPv4 only, IPv6 only, or IPv4 and IPv6.
When adding an IPv6 access rule, the source and destination can only be IPv6 address objects.
IPSec VPNs can be configured for IPv6 in a similar manner to IPv4 VPNs after selecting the IPv6 option in the View IP Version radio button at the top left of the VPN > Settings page.
There are certain VPN features that are currently not supported for IPv6, including:
IKEv2 is supported, while IKE is currently not supported
GroupVPN is not supported
DHCP Over VPN is not supported.
When configuring an IPv6 VPN policy, on the General tab the gateways must be configured using IPv6 addresses. FQDN is not supported. When configuring IKE authentication, IPV6 addresses can be used for the local and peer IKE IDs.
Note DHCP Over VPN and L2TP Server are not supported for IPv6.
On the Network tab of the VPN policy, IPV6 address objects (or address groups that contain only IPv6 address objects) must be selected for the Local Network and Remote Network.
DHCP Over VPN is not supported, thus the DHCP options for protected network are not available.
The Any address option for Local Networks and the Tunnel All option for Remote Networks are removed. Select an all zero IPv6 Network address object could be selected for the same functionality and behavior.
On the Proposals tab, the configuration is identical for IPv6 and IPv4, except for the fact that IPv6 only support IKEv2 mode.
On the Advanced tab, only Enable Keep Alive and the IKEv2 Settings can be configured for IPv6 VPN policies.
Note Because an interface may have multiple IPv6 address, sometimes the local address of the tunnel may vary periodically. If the user needs a consistent IP address, configure the VPN policy to be bound to an interface instead of Zone, and specify the address manually. The address must be one of IPv6 addresses for that interface.
SSL VPN Configuration for IPv6
SonicOS supports NetExtender connections for users with IPv6 addresses. On the SSLVPN > Client Settings page, first configure the traditional IPv6 IP address pool, and then configure an IPv6 IP Pool. Clients will be assigned two internal addresses: one IPv4 and one IPv6.
Note IPv6 DNS/Wins Server are not supported
On the SSLVPN > Client Routes page, user can select a client routes from the drop-down list of all address objects including all the pre-defined IPv6 address objects.
Note IPv6 FQDN is supported.
IPv6 Diagnostics and Monitoring
SonicOS provides a full compliment of diagnostic tools for IPv6, including the following:
Packet Capture fully supports IPv6.
IPv6 keywords can be used to filter the packet capture.
The ping tool includes a new Ping IPv6 network preferred option.
When pinging a domain name, it uses the first IP address that is returned and shows the actual pinging address. If both an IPv4 and IPv6 address are returned, by default, the firewall pings the IPv4 address.
If the Ping IPv6 network preferred option is enabled, the firewall will ping the IPv6 address.
IPv6 DNS Lookup and Reverse Name Lookup
When performing IPv6 DNS Lookup or IPv6 Reverse Name Lookup, you must enter the DNS server address. Either an IPv6 or IPv4 address can be used.