VPN_vpnSettingsView
The VPN > Settings page provides the features for configuring your VPN policies. You can configure site-to-site VPN policies and GroupVPN policies from this page.
A Virtual Private Network (VPN) provides a secure connection between two or more computers or protected networks over the public Internet. It provides authentication to ensure that the information is going to and from the correct parties. It provides security to protect the information from viewing or tampering en route.
Prior to the invention of Internet Protocol Security (IPsec) and Secure Socket Layer (SSL), secure connections between remote computers or networks required a dedicated line or satellite link. This was both inflexible and expensive.
A VPN creates a connection with similar reliability and security by establishing a secure tunnel through the Internet. Because this tunnel is not a physical connection, it is more flexible--you can change it at any time to add more nodes, change the nodes, or remove it altogether. It is also far less costly, because it uses the existing Internet infrastructure.
There are two main types of VPN in popular use today:
• IPsec VPN: IPsec is a set of protocols for security at the packet processing layer of network communication. An advantage of IPsec is that security arrangements can be handled without requiring changes to individual user computers. SonicOS supports the creation and management of IPsec VPNs.
IPsec provides two choices of security service: Authentication Header (AH), which essentially allows authentication of the sender of data, and Encapsulating Security Payload (ESP), which supports both authentication of the sender and encryption of data as well. The specific information associated with each of these services is inserted into the packet in a header that follows the IP packet header.
• SSL VPN: Secure Socket Layer (SSL) is a protocol for managing the security of a message transmission on the Internet, usually by HTTPS. SSL uses a program layer located between the Internet's Hypertext Transfer Protocol (HTTP) and Transport Control Protocol (TCP) layers. SSL uses the public-and-private key encryption system from RSA, which also includes the use of a digital certificate. An SSL VPN uses SSL to secure the VPN tunnel.
One advantage of SSL VPN is that SSL is built into most Web Browsers. No special VPN client software or hardware is required.
Note Dell SonicWALL makes SSL VPN devices that you can use in concert with or independently of a Dell SonicWALL network security appliance running SonicOS. For information on Dell SonicWALL SSL VPN appliances, see the Dell SonicWALL Website: http://www.sonicwall.com/us/products/Secure_Remote_Access.html
IPsec VPN traffic is secured in two stages:
• Authentication: The first phase establishes the authenticity of the sender and receiver of the traffic using an exchange of the public key portion of a public-private key pair. This phase must be successful before the VPN tunnel can be established.
• Encryption: The traffic in the VPN tunnel is encrypted, using an encryption algorithm such as AES or 3DES.
Unless you use a manual key (which must be typed identically into each node in the VPN) The exchange of information to authenticate the members of the VPN and encrypt/decrypt the data uses the Internet Key Exchange (IKE) protocol for exchanging authentication information (keys) and establishing the VPN tunnel. SonicOS supports two versions of IKE, version 1 and version 2.
IKE version 1
IKE version 1 uses a two phase process to secure the VPN tunnel.
• IKE Phase 1 is the authentication phase. The nodes or gateways on either end of the tunnel authenticate with each other, exchange encryption/decryption keys, and establish the secure tunnel.
• IKE Phase 2 is the negotiation phase. Once authenticated, the two nodes or gateways negotiate the methods of encryption and data verification (using a hash function) to be used on the data passed through the VPN and negotiate the number of secure associations (SAs) in the tunnel and their lifetime before requiring renegotiation of the encryption/decryption keys.
IKE Phase 1
In IKE v1, there are two modes of exchanging authentication information: Main Mode and Aggressive Mode.
Main Mode: The node or gateway initiating the VPN queries the node or gateway on the receiving end, and they exchange authentication methods, public keys, and identity information. This usually requires six messages back and forth. The order of authentication messages in Main Mode is:
1. The initiator sends a list of cryptographic algorithms the initiator supports.
2. The responder replies with a list of supported cryptographic algorithms.
3. The initiator send a public key (part of a Diffie-Hellman public/private key pair) for the first mutually supported cryptographic algorithm.
4. The responder replies with the public key for the same cryptographic algorithm.
5. The initiator sends identity information (usually a certificate).
6. The responder replies with identity information.
Aggressive Mode: To reduce the number of messages exchanged during authentication by half, the negotiation of which cryptographic algorithm to use is eliminated. The initiator proposes one algorithm and the responder replies if it supports that algorithm:
1. The initiator proposes a cryptographic algorithm to use and sends its public key.
2. The responder replies with a public key and identity proof.
3. The initiator sends an identification proof. After authenticating, the VPN tunnel is established with two SAs, one from each node to the other.
IKE Phase 2
In IKE phase 2, the two parties negotiate the type of security to use, which encryption methods to use for the traffic through the tunnel (if needed), and negotiate the lifetime of the tunnel before re-keying is needed.
The two types of security for individual packets are:
• Encryption Secured Payload (ESP), in which the data portion of each packet is encrypted using a protocol negotiated between the parties.
• Authentication Header (AH), in which the header of each packet contains authentication information to ensure the information is authenticated and has not been tampered with. No encryption is used for the data with AH.
SonicOS supports the following encryption methods for Traffic through the VPN.
• DES
• 3DES
• AES-128
• AES-192
• AES-256
You can find more information about IKE v1 in the three specifications that define initially define IKE, RFC 2407, RFC 2408, and RFC 2409, available on the Web at:
• http://www.faqs.org/rfcs/rfc2407.html
• http://www.faqs.org/rfcs/rfc2408.html
• http://www.faqs.org/rfcs/rfc2409.html
IKE version 2
IKE version 2 is a newer protocol for negotiating and establishing security associations. IKEv2 features improved security, a simplified architecture, and enhanced support for remote users.
IKEv2 is the default proposal type for new VPN policies.
Secondary gateways are supported with IKEv2.
IKEv2 is not compatible with IKE v1. If using IKEv2, all nodes in the VPN must use IKEv2 to establish the tunnels.
DHCP over VPN is not supported in IKEv2.
IKEv2 has the following advantages over IKEv1:
• More secure
• More reliable
• Simpler
• Faster
• Extensible
• Fewer message exchanges to establish connections
• EAP Authentication support
• MOBIKE support
• Built-in NAT traversal
• Keep Alive is enabled as default
IKEv2 supports IP address allocation and EAP to enable different authentication methods and remote access scenarios. Using IKEv2 greatly reduces the number of message exchanges needed to establish an SA over IKE v1 Main Mode, while being more secure and flexible than IKE v1 Aggressive Mode. This reduces the delays during re-keying. As VPNS grow to include more and more tunnels between multiple nodes or gateways, IKEv2 reduces the number of SAs required per tunnel, thus reducing required bandwidth and housekeeping overhead.
SAs in IKEv2 are called Child SAs and can be created, modified, and deleted independently at any time during the life of the VPN tunnel.
Initialization and Authentication in IKE v2
IKE v2 initializes a VPN tunnel with a pair of message exchanges (two message/response pairs).
• Initialize communication: The first pair of messages (IKE_SA_INIT) negotiate cryptographic algorithms, exchange nonces (random values generated and sent to guard against repeated messages), and perform a public key exchange.
a. Initiator sends a list of supported cryptographic algorithms, public keys, and a nonce.
b. Responder sends the selected cryptographic algorithm, the public key, a nonce, and an authentication request.
• Authenticate: The second pair of messages (IKE_AUTH) authenticate the previous messages, exchange identities and certificates, and establish the first CHILD_SA. Parts of these messages are encrypted and integrity protected with keys established through the IKE_SA_INIT exchange, so the identities are hidden from eavesdroppers and all fields in all the messages are authenticated.
a. Initiator sends identity proof, such as a shared secret or a certificate, and a request to establish a child SA.
b. Responder sends the matching identity proof and completes negotiation of a child SA.
Negotiating SAs in IKE v2
This exchange consists of a single request/response pair, and was referred to as a phase 2 exchange in IKE v1. It may be initiated by either end of the SA after the initial exchanges are completed.
All messages following the initial exchange are cryptographically protected using the cryptographic algorithms and keys negotiated in the first two messages of the IKE exchange.
Either endpoint may initiate a CREATE_CHILD_SA exchange, so in this section the term “initiator” refers to the endpoint initiating this exchange.
1. Initiator sends a child SA offer and, if the data is to be encrypted, the encryption method and the public key.
2. Responder sends the accepted child SA offer and, if encryption information was included, a public key.
Note You can find more information about IKE v2 in the specification, RFC 4306, available on the Web at: http://www.ietf.org/rfc/rfc4306.txt
For information on configuring VPNs in SonicOS, see:
• Configuring GroupVPN Policies
• Site-to-Site VPN Configurations
• Creating Site-to-Site VPN Policies
• VPN Auto-Added Access Rule Control
For an overview of VPNs in SonicOS Enhanced, see VPN > Settings.
SonicWALL VPN, based on the industry-standard IPsec VPN implementation, provides a easy-to-setup, secure solution for connecting mobile users, telecommuters, remote offices and partners via the Internet. Mobile users, telecommuters, and other remote users with broadband (DSL or cable) or dialup Internet access can securely and easily access your network resources with the Dell SonicWALL Global VPN Client and GroupVPN on your firewall. Remote office networks can securely connect to your network using site-to-site VPN connections that enable network-to- network VPN connections.
The GroupVPN provides automatic VPN policy provisioning for Global VPN Clients. The GroupVPN feature on the Dell SonicWALL network security appliance and the Global VPN Client dramatically streamline VPN deployment and management. Using the Client Policy Provisioning technology, you define the VPN policies for Global VPN Client users. This policy information automatically downloads from the firewall (VPN Gateway) to Global VPN Clients, saving remote users the burden of provisioning VPN connections.
You can configure GroupVPN or site-to-site VPN tunnels using the Management Interface. You can define up to four GroupVPN policies, one for each zone. You can also create multiple site-to-site VPN. The maximum number of policies you can add depends on your SonicWALL model.
Note Remote users must be explicitly granted access to network resources on the Users > Local Users or Users > Local Groups pages. When configuring local users or local groups, the VPN Access tab affects the ability of remote clients using GVC connecting to GroupVPN; it also affects remote users using NetExtender, and SSL VPN Virtual Office bookmarks to access network resources. To allow GVC, NetExtender, or Virtual Office users to access a network resource, the network address objects or groups must be added to the “allow” list on the VPN Access tab.
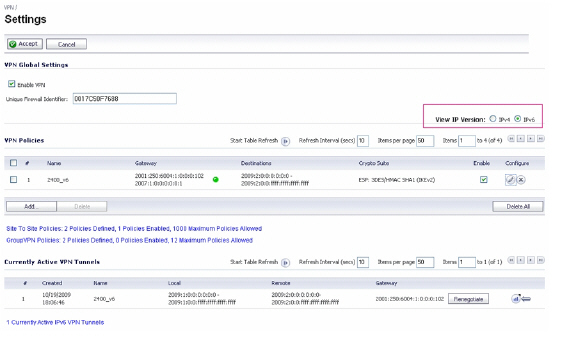
The Global VPN Settings section of the VPN > Settings page displays the following information:
Enable VPN must be selected to allow VPN policies through the Dell SonicWALL security policies.
• Unique Firewall Identifier - the default value is the serial number of the firewall. You can change the Identifier, and use it for configuring VPN tunnels.
All existing VPN policies are displayed in the VPN Policies table. Each entry displays the following information:
Name: Displays the default name or user-defined VPN policy name.
• Gateway: Displays the IP address of the remote firewall. If 0.0.0.0 is used, no Gateway is displayed.
• Destinations: Displays the IP addresses of the destination networks.
• Crypto Suite: Displays the type of encryption used for the VPN policy.
• Enable: Selecting the check box enables the VPN Policy. Clearing the check box disables it.
• Configure: Clicking the Edit icon allows you to edit the VPN policy. Clicking the Delete ![]() icon allows you to delete the VPN policy. The predefined GroupVPN policies cannot be deleted, so the Delete icons are dimmed. GroupVPN policies also have a Disk icon for exporting the VPN policy configuration as a file for local installation by SonicWALL Global VPN Clients.
icon allows you to delete the VPN policy. The predefined GroupVPN policies cannot be deleted, so the Delete icons are dimmed. GroupVPN policies also have a Disk icon for exporting the VPN policy configuration as a file for local installation by SonicWALL Global VPN Clients.
The number of VPN policies defined, policies enabled, and the maximum number of Policies allowed is displayed below the table. You can define up to 4 GroupVPN policies, one for each zone. These GroupVPN policies are listed by default in the VPN Policies table as WAN GroupVPN, LAN GroupVPN, DMZ GroupVPN, and WLAN GroupVPN. Clicking on the edit icon in the Configure column for the GroupVPN displays the VPN Policy window for configuring the GroupVPN policy.
Below the VPN Policies table are the following buttons:
• Add - Accesses the VPN Policy window to configure site-to-site VPN policies.
• Delete - Deletes the selected (checked box before the VPN policy name in the Name column. You cannot delete the GroupVPN policies.
• Delete All - Deletes all VPN policies in the VPN Policies table except the default GroupVPN policies.
Navigating and Sorting the VPN Policies Entries
The VPN Policies table provides easy pagination for viewing a large number of VPN policies. You can navigate a large number of VPN policies listed in the VPN Policies table by using the navigation control bar located at the top right of the VPN Policies table. Navigation control bar includes four buttons. The far left button displays the first page of the table. The far right button displays the last page. The inside left and right arrow buttons moved the previous or next page respectively.
You can enter the policy number (the number listed before the policy name in the # Name column) in the Items field to move to a specific VPN policy. The default table configuration displays 50 entries per page. You can change this default number of entries for tables on the System > Administration page.
You can sort the entries in the table by clicking on the column header. The entries are sorted by ascending or descending order. The arrow to the right of the column entry indicates the sorting status. A down arrow means ascending order. An up arrow indicates a descending order.
A list of currently active VPN tunnels is displayed in this section. The table lists the name of the VPN Policy, the local LAN IP addresses, and the remote destination network IP addresses as well as the peer gateway IP address.
Click the Renegotiate button to force the VPN Client to renegotiate the VPN tunnel.
Viewing VPN Tunnel Statistics
The table in the Currently Active VPN Tunnels section displays these statistics for each tunnel:
• Create Time: The date and time the tunnel came into existence.
• Tunnel valid until: The time when the tunnel expires and is force to renegotiate.
• Packets In: The number of packets received from this tunnel.
• Packets Out: The number of packets sent out from this tunnel.
• Bytes In: The number of bytes received from this tunnel.
• Bytes Out: The number of bytes sent out from this tunnel.
• Fragmented In: The number of fragmented packets received from this tunnel.
• Fragmented Out: The number of fragmented packets sent out from this tunnel.
For detailed information on configuring VPNs in SonicOS, see:
• Configuring GroupVPN Policies
• Site-to-Site VPN Configurations
• Creating Site-to-Site VPN Policies
• VPN Auto-Added Access Rule Control
 For complete information on the SonicOS implementation of IPv6, see IPv6.
For complete information on the SonicOS implementation of IPv6, see IPv6.
IPSec VPNs can be configured for IPv6 in a similar manner to IPv4 VPNs after selecting the IPv6 option in the View IP Version radio button at the top right of the VPN Policies section.
There are certain VPN features that are currently not supported for IPv6, including:
• IKEv2 is supported, while IKEv1 is currently not supported
• GroupVPN is not supported
• DHCP Over VPN is not supported.
Topics:
When configuring an IPv6 VPN policy, on the General tab, the gateways must be configured using IPv6 addresses. FQDN is not supported. When configuring IKE authentication, IPV6 addresses can be used for the local and peer IKE IDs.
Note DHCP Over VPN and L2TP Server are not supported for IPv6.
On the Network tab of the VPN policy, IPV6 address objects (or address groups that contain only IPv6 address objects) must be selected for the Local Networks and Remote Networks.
DHCP Over VPN is not supported, thus the DHCP options for protected network are not available.
The Any address option for Local Networks and the Tunnel All option for Remote Networks are removed. An all-zero IPv6 Network address object could be selected for the same functionality and behavior.
On the Proposals tab, the configuration is identical for IPv6 and IPv4, except IPv6 only supports IKEv2 mode.
The Advanced tab for IPv6 is similar to that of IPv4, with only these options being IP-version specific:
|
| ||||||||||||||||||||||||||
Because an interface may have multiple IPv6 address, sometimes the local address of the tunnel may vary periodically. If a user needs a consistent IP address, configure the VPN policy to be bound to an interface instead of a Zone, and then specify the address manually. The address must be one of the IPv6 addresses for that interface.
GroupVPN policies facilitate the set up and deployment of multiple Global VPN Clients by the firewall administrator. GroupVPN is only available for Global VPN Clients and it is recommended you use XAUTH/RADIUS or third party certificates in conjunction with the Group VPN for added security.
From the Network > Zones page, you can create GroupVPN policies for any zones. SonicOS provides two default GroupVPN policies for the WAN and WLAN zones, as these are generally the less trusted zones. These two default GroupVPN policies are listed in the VPN Policies panel on the VPN > Settings page:
• WAN GroupVPN
• WLAN GroupVPN
In the VPN Policy dialog, from the Authentication Method menu, you can choose either the IKE using Preshared Secret option or the IKE using 3rd Party Certificates option for your IPsec Keying Mode.
SonicOS supports the creation and management of IPsec VPNs.
Topics:
• Configuring GroupVPN with IKE using Preshared Secret on the WAN Zone
• Configuring GroupVPN with IKE using 3rd Party Certificates
• Exporting a VPN Client Policy
Configuring GroupVPN with IKE using Preshared Secret on the WAN Zone
To configure the WAN GroupVPN, follow these steps:
1. Click the edit icon for the WAN GroupVPN entry. The VPN Policy dialog is displayed.
2. In the General tab, IKE using Preshared Secret is the default setting for Authentication Method. A Shared Secret is automatically generated by the firewall in the Shared Secret field, or you can generate your own shared secret. Shared Secrets must be a minimum of four characters. You cannot change the name of any GroupVPN policy.
3. Click the Proposals tab to continue the configuration process.
4. In the IKE (Phase 1) Proposal section, use the following settings:
• Select the DH Group from the DH Group menu:
– Group 1, Group 2, Group 5, or Group 14
– 256-Bit Random ECP Group, 384-Bit Random ECP Group, 521-Bit Random ECP Group, 192-Bit Random ECP Group, or 224-Bit Random ECP Group
Note The Windows 2000 L2TP client and Windows XP L2TP client can only work with DH Group 2. They are incompatible with DH Groups 1 and 5.
• Select DES, 3DES, AES-128, AES-192, or AES-256 from the Encryption menu.
• Select the desired authentication method from the Authentication menu.
• Enter a value in the Life Time (seconds) field. The default setting of 28800 forces the tunnel to renegotiate and exchange keys every 8 hours.
5. In the IPsec (Phase 2) Proposal section, select the following settings:
• Select the desired protocol from the Protocol menu.
• Select 3DES, AES-128, AES-192, or AES-256 from the Encryption menu.
• Select the desired authentication method from the Authentication menu.
• Select Enable Perfect Forward Secrecy if you want an additional Diffie-Hellman key exchange as an added layer of security. Select Group 2 from the DH Group menu.
Note The Windows 2000 L2TP client and Windows XP L2TP client can only work with DH Group 2. They are incompatible with DH Groups 1 and 5.
• Enter a value in the Life Time (seconds) field. The default setting of 28800 forces the tunnel to renegotiate and exchange keys every 8 hours.
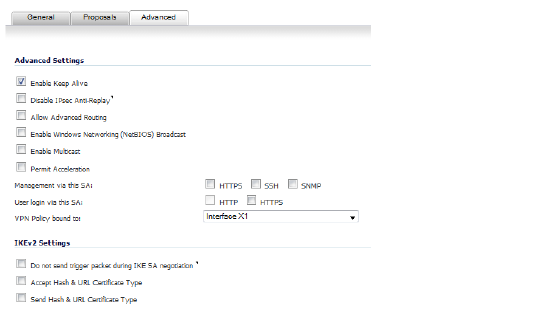
6. Click the Advanced tab.
7. Select any of the following optional settings you want to apply to your GroupVPN policy:
Advanced Settings
• Disable IPsec Anti-Replay - Stops packets with duplicate sequence numbers from being dropped.
• Enable Windows Networking (NetBIOS) broadcast - Allows access to remote network resources by browsing the Windows® Network Neighborhood.
• Enable Multicast - Enables IP multicasting traffic, such as streaming audio (including VoIP) and video applications, to pass through the VPN tunnel.
• Accept Multiple Proposals for Clients - Allows multiple proposals for clients, such as the IKE (Phase 1) Proposal or the IKE (Phase 2) Proposal, to be accepted.
• Management via this SA: - If using the VPN policy to manage the firewall, select the management method, either HTTP, SSH, or HTTPS.
Note SSH is valid for IPv4 only.
• Default Gateway - Allows you to specify the IP address of the default network route for incoming IPsec packets for this VPN policy. Incoming packets are decoded by the firewall and compared to static routes configured in the firewall.
As packets can have any IP address destination, it is impossible to configure enough static routes to handle the traffic. For packets received via an IPsec tunnel, the firewall looks up a route. If no route is found, the security appliance checks for a Default Gateway. If a Default Gateway is detected, the packet is routed through the gateway. Otherwise, the packet is dropped.
Client Authentication
• Require Authentication of VPN Clients via XAUTH - Requires that all inbound traffic on this VPN tunnel is from an authenticated user. Unauthenticated traffic is not allowed on the VPN tunnel. The Trusted users group is selected by default. You can select another user group or Everyone from User Group for XAUTH users from the User group for XAUTH users menu.
• Allow Unauthenticated VPN Client Access - Allows you to enable unauthenticated VPN client access. If you clear Require Authentication of VPN Clients via XAUTH, the Allow Unauthenticated VPN Client Access menu is activated. Select an Address Object or Address Group from menu of predefined options, or select Create new address object or Create new address group to create a new one.
8. Click the Client tab, select any of the following settings you want to apply to your GroupVPN policy.
User Name and Password Caching
• Cache XAUTH User Name and Password on Client - Allows the Global VPN Client to cache the user name and password.
– Never - Global VPN Client is not allowed to cache the username and password. The user will be prompted for a username and password when the connection is enabled, and also every time there is an IKE Phase 1 rekey.
– Single Session - Global VPN Client user prompted for username and password each time the connection is enabled and will be valid until the connection is disabled. The username and password is used through IKE Phase 1 rekey.
– Always - Global VPN Client user prompted for username and password only once when connection is enabled. When prompted, the user will be given the option of caching the username and password.
Client Connections
• Virtual Adapter Settings - The use of the Virtual Adapter by the Global VPN Client (GVC) is dependent upon a DHCP server, either the internal SonicOS or a specified external DHCP server, to allocate addresses to the Virtual Adapter.
In instances where predictable addressing was a requirement, it is necessary to obtain the MAC address of the Virtual Adapter, and to create a DHCP lease reservation. To reduce the administrative burden of providing predictable Virtual Adapter addressing, you can configure the GroupVPN to accept static addressing of the Virtual Adapter's IP configuration.
Note This feature requires the use of SonicWALL GVC.
– None - A Virtual Adapter will not be used by this GroupVPN connection.
– DHCP Lease - The Virtual Adapter will obtain its IP configuration from the DHCP Server only, as configure in the VPN > DHCP over VPN page.
– DHCP Lease or Manual Configuration - When the GVC connects to the firewall, the policy from the firewall instructs the GVC to use a Virtual Adapter, but the DHCP messages are suppressed if the Virtual Adapter has been manually configured. The configured value is recorded by the firewall so that it can proxy ARP for the manually assigned IP address. By design, there are currently no limitations on IP address assignments for the Virtual Adapter. Only duplicate static addresses are not permitted.
• Allow Connections to - Client network traffic matching destination networks of each gateway is sent through the VPN tunnel of that specific gateway.
– This Gateway Only - Allows a single connection to be enabled at a time. Traffic that matches the destination networks as specified in the policy of the gateway is sent through the VPN tunnel. If this option is selected along with Set Default Route as this Gateway, then the Internet traffic is also sent through the VPN tunnel. If this option is selected without selecting Set Default Route as this Gateway, then the Internet traffic is blocked.
– All Secured Gateways - Allows one or more connections to be enabled at the same time. Traffic matching the destination networks of each gateway is sent through the VPN tunnel of that specific gateway. If this option is selected along with Set Default Route as this Gateway, then Internet traffic is also sent through the VPN tunnel. If this option is selected without Set Default Route as this Gateway, then the Internet traffic is blocked. Only one of the multiple gateways can have Set Default Route as this Gateway enabled.
– Split Tunnels - Allows the VPN user to have both local Internet connectivity and VPN connectivity.
• Set Default Route as this Gateway - Enable this check box if all remote VPN connections access the Internet through this VPN tunnel. You can only configure one VPN policy to use this setting.
Client Initial Provisioning
• Use Default Key for Simple Client Provisioning - Uses Aggressive mode for the initial exchange with the gateway and VPN clients uses a default Preshared Key for authentication.
9. Click OK.
Configuring GroupVPN with IKE using 3rd Party Certificates
To configure GroupVPN with IKE using 3rd Party Certificates, follow these steps:
CAUTION Before configuring GroupVPN with IKE using 3rd Party Certificates, your certificates must be installed on the firewall.
1. In the VPN > Settings page click the edit icon under Configure. The VPN Policy window is displayed.
In the Security Policy section, select IKE using 3rd Party Certificates from the Authentication Method drop-down menu.
Note The VPN policy name is GroupVPN by default and cannot be changed.
3. Select a certificate for the firewall from the Gateway Certificate menu.
4. Select one of the following Peer ID types from the Peer ID Type menu:
• Email ID and Domain Name - The Email ID and Domain Name types are based on the certificate's Subject Alternative Name field, which is not contained in all certificates by default. If the certificate does not contain a Subject Alternative Name field, this filter will not work.
The Email ID and Domain Name filters can contain a string or partial string identifying the acceptable range required. The strings entered are not case sensitive and can contain the wild card characters * (for more than 1 character) and ? (for a single character). For example, the string *@sonicwall.com when Email ID is selected, would allow anyone with an email address that ended in sonicwall.com to have access; the string *sv.us.sonicwall.com when Domain Name is selected, would allow anyone with a domain name that ended in sv.us.sonicwall.com to have access.
• Distinguished Name - This is based on the certificate’s Subject Distinguished Name field, which is contained in all certificates by default.
The format of any Subject Distinguished Name is determined by the issuing Certificate Authority. Common fields are Country (C=), Organization (O=), Organizational Unit (OU=), Common Name (CN=), Locality (L=), and vary with the issuing Certificate Authority. The actual Subject Distinguished Name field in an X.509 Certificate is a binary object which must be converted to a string for matching purposes. The fields are separated by the forward slash character, for example: /C=US/O=SonicWALL, Inc./OU=TechPubs/CN=Joe Pub
Up to three organizational units can be specified. The usage is c=*;o=*;ou=*;ou=*;ou=*;cn=*. The final entry does not need to contain a semi-colon. You must enter at least one entry, for example, c=us.
5. Enter the Peer ID filter in the Peer ID Filter field.
6. Check Allow Only Peer Certificates Signed by Gateway Issuer to specify that peer certificates must be signed by the issuer specified in the Gateway Certificate menu.
7. Click on the Proposals tab.
8. In the IKE (Phase 1) Proposal section, select the following settings:
• Select the DH Group from the DH Group menu.
– Group 1, Group 2, Group 5, or Group 14
– 256-Bit Random ECP Group, 384-Bit Random ECP Group, 521-Bit Random ECP Group, 192-Bit Random ECP Group, or 224-Bit Random ECP Group
Note The Windows 2000 L2TP client and Windows XP L2TP client can only work with DH Group 2. They are incompatible with DH Groups 1 and 5.
• Select 3DES, AES-128, AES-192, or AES-256 from the Encryption menu.
• Select the desired authentication method from the Authentication menu.
• Enter a value in the Life Time (seconds) field. The default setting of 28800 forces the tunnel to renegotiate and exchange keys every 8 hours.
9. In the IPsec (Phase 2) Proposal section, select the following settings:
• Select the desired protocol from the Protocol menu.
• Select 3DES, AES-128, AES-192, or AES-256 from the Encryption menu.
• Select the desired authentication method from the Authentication menu.
• Select Enable Perfect Forward Secrecy if you want an additional Diffie-Hellman key exchange as an added layer of security. Select Group 2 from the DH Group menu.
Note The Windows 2000 L2TP client and Windows XP L2TP client can only work with DH Group 2. They are incompatible with DH Groups 1 and 5.
• Enter a value in the Life Time (seconds) field. The default setting of 28800 forces the tunnel to renegotiate and exchange keys every 8 hours.
10. Click on the Advanced tab and select any of the following optional settings that you want to apply to your GroupVPN Policy:
• Enable Windows Networking (NetBIOS) broadcast - Allows access to remote network resources by browsing the Windows Network Neighborhood.
• Enable Multicast - Enables IP multicasting traffic, such as streaming audio (including VoIP) and video applications, to pass through the VPN tunnel.
• Management via this SA - If using the VPN policy to manage the firewall, select the management method, either HTTP, SSH, or HTTPS.
Note SSH is valid for IPv4 only.
• Default Gateway - Used at a central site in conjunction with a remote site using the Route all Internet traffic through this SA check box. Default LAN Gateway allows you to specify the IP address of the default LAN route for incoming IPsec packets for this SA.
Incoming packets are decoded by the firewall and compared to static routes configured in the firewall. Since packets can have any IP address destination, it is impossible to configure enough static routes to handle the traffic. For packets received via an IPsec tunnel, the firewall looks up a route for the LAN. If no route is found, the firewall checks for a Default LAN Gateway. If a Default LAN Gateway is detected, the packet is routed through the gateway. Otherwise, the packet is dropped.
• Enable OCSP Checking and OCSP Responder URL - Enables use of Online Certificate Status Protocol (OCSP) to check VPN certificate status and specifies the URL where to check certificate status. See Using OCSP with Dell SonicWALL Network Security Appliances.
• Require Authentication of VPN Clients via XAUTH - Requires that all inbound traffic on this VPN policy is from an authenticated user. Unauthenticated traffic is not allowed on the VPN tunnel.
• User group for XAUTH users - Allows you to select a defined user group for authentication.
• Allow Unauthenticated VPN Client Access - Allows you to specify network segments for unauthenticated Global VPN Client access.
11. Click on the Client tab and select any of the following boxes that you want to apply to Global VPN Client provisioning:
• Cache XAUTH User Name and Password - Allows the Global VPN Client to cache the user name and password. Select from:
– Never - Global VPN Client is not allowed to cache username and password. The user will be prompted for a username and password when the connection is enabled and also every time there is an IKE phase 1 rekey.
– Single Session - The user will be prompted for username and password each time the connection is enabled and will be valid until the connection is disabled. This username and password is used through IKE phase 1 rekey.
– Always - The user will be prompted for username and password only once when connection is enabled. When prompted, the user will be given the option of caching the username and password.
• Virtual Adapter Settings - The use of the Virtual Adapter by the Global VPN Client (GVC) is dependent upon a DHCP server, either the internal SonicOS or a specified external DHCP server, to allocate addresses to the Virtual Adapter.
In instances where predictable addressing was a requirement, it is necessary to obtain the MAC address of the Virtual Adapter, and to create a DHCP lease reservation. To reduce the administrative burden of providing predictable Virtual Adapter addressing, you can configure the GroupVPN to accept static addressing of the Virtual Adapter's IP configuration. This feature requires the use of SonicWALL GVC.
– None - A Virtual Adapter will not be used by this GroupVPN connection.
– DHCP Lease - The Virtual Adapter will obtain its IP configuration from the DHCP Server only, as configure in the VPN > DHCP over VPN page.
– DHCP Lease or Manual Configuration - When the GVC connects to the firewall, the policy from the firewall instructs the GVC to use a Virtual Adapter, but the DHCP messages are suppressed if the Virtual Adapter has been manually configured. The configured value is recorded by the firewall so that it can proxy ARP for the manually assigned IP address. By design, there are currently no limitations on IP address assignments for the Virtual Adapter. Only duplicate static addresses are not permitted.
• Allow Connections to - Client network traffic matching destination networks of each gateway is sent through the VPN tunnel of that specific gateway.
– This Gateway Only - Allows a single connection to be enabled at a time. Traffic that matches the destination networks as specified in the policy of the gateway is sent through the VPN tunnel. If this option is selected along with Set Default Route as this Gateway, then the Internet traffic is also sent through the VPN tunnel. If this option is selected without selecting Set Default Route as this Gateway, then the Internet traffic is blocked.
– All Secured Gateways - Allows one or more connections to be enabled at the same time. Traffic matching the destination networks of each gateway is sent through the VPN tunnel of that specific gateway.
If this option is selected along with Set Default Route as this Gateway, then Internet traffic is also sent through the VPN tunnel. If this option is selected without Set Default Route as this Gateway, then the Internet traffic is blocked.
Note Only one of the multiple gateways can have Set Default Route as this Gateway enabled.
– Split Tunnels - Allows the VPN user to have both local Internet connectivity and VPN connectivity.
• Set Default Route as this Gateway - Enable this check box if all remote VPN connections access the Internet through this SA. You can only configure one SA to use this setting.
• Use Default Key for Simple Client Provisioning - Uses Aggressive mode for the initial exchange with the gateway and VPN clients uses a default Preshared Key for authentication.
12. Click OK.
If you want to export the Global VPN Client configuration settings to a file for users to import into their Global VPN Clients, follow these instructions:
CAUTION The GroupVPN SA must be enabled on the firewall to export a configuration file.
1. Click the Export ![]() icon in the Configure column for the GroupVPN entry in the VPN Policies table. The Export VPN Client Policy window appears.
icon in the Configure column for the GroupVPN entry in the VPN Policies table. The Export VPN Client Policy window appears.
2. rcf format is required for SonicWALL Global VPN Clients is selected by default. Files saved in the rcf format can be password encrypted. The firewall provides a default file name for the configuration file, which you can change.
3. Click Yes. The VPN Policy Export window appears.
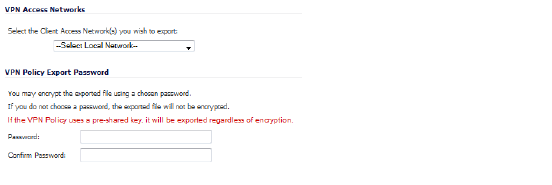
4. Select a VPN Access Networks from the Select the client Access Network(s) you wish to export drop-down menu.
5. Type a password in the Password field and reenter it in the Confirm Password field, if you want to encrypt the exported file. If you choose not to enter a password, the exported file is not encrypted.
6. Click Submit. If you did not enter a password, a message appears confirming your choice.
7. Click OK. You can change the configuration file before saving.
8. Save the file.
9. Click Close.
The file can be saved or sent electronically to remote users to configure their Global VPN Clients.
Site-to-Site VPN Configurations
When designing VPN connections, be sure to document all pertinent IP addressing information and create a network diagram to use as a reference. A sample planning sheet is provided on the next page. The firewall must have a routable WAN IP address whether it is dynamic or static. In a VPN network with dynamic and static IP addresses, the VPN gateway with the dynamic address must initiate the VPN connection.
Site-to-Site VPN configurations can include the following options:
• Branch Office (Gateway to Gateway) - A SonicWALL is configured to connect to another SonicWALL via a VPN tunnel. Or, a SonicWALL is configured to connect via IPsec to another manufacturer’s firewall.
• Hub and Spoke Design - All SonicWALL VPN gateways are configured to connect to a central hub, such as a corporate firewall. The hub must have a static IP address, but the spokes can have dynamic IP addresses. If the spokes are dynamic, the hub must be a Dell SonicWALL network security appliance.
• Mesh Design - All sites connect to all other sites. All sites must have static IP addresses.
Creating Site-to-Site VPN Policies
You can create or modify existing VPN policies using the VPN Policy window. Clicking the Add button under the VPN Policies table displays the VPN Policy window for configuring the following IPsec Keying mode VPN policies:
• Configuring a VPN Policy with IKE using Preshared Secret
• Configuring a VPN Policy using Manual Key
• Configuring a VPN Policy with IKE using a Third Party Certificate
This section also contains information on configuring a static route to act as a failover in case the VPN tunnel goes down. See Configuring VPN Failover to a Static Route for more information.
Tip Informational videos with Site-to-Site VPN configuration examples are available online. For example, see How to Create a Site to Site VPN in Main Mode using Preshared Secret or How to Create Aggressive Mode Site to Site VPN using Preshared Secret.
Additional videos are available at: https://support.software.dell.com/videos-product-select.
Configuring a VPN Policy with IKE using Preshared Secret
To configure a VPN Policy using Internet Key Exchange (IKE), follow the steps below:
1. Go to the VPN > Settings page. The VPN Policy page is displayed.
2. Click the Add button. The VPN Policy dialog appears.
3. From the Policy Type drop-down menu on the General tab, select the type of policy that you want to create:
• Site to Site
• Tunnel Interface
Note If you select Tunnel Interface for the Policy Type, the IPsec Secondary Gateway Name or Address option and the Network tab are not available.
4. Select IKE using Preshared Secret from the Authentication Method drop-down menu.
5. Enter a name for the policy in the Name field.
6. Enter the host name or IP address of the remote connection in the IPsec Primary Gateway Name or Address field.
7. If the Remote VPN device supports more than one endpoint, you may optionally enter a second host name or IP address of the remote connection in the IPsec Secondary Gateway Name or Address field.
Note If you selected Tunnel Interface for the Policy Type, this option is not available.
8. In the IKE Authentication section, enter in the Shared Secret and Confirm Shared Secret fields a Shared Secret password to be used to setup the Security Association. The Shared Secret must be at least 4 characters long, and should comprise both numbers and letters.
9. By default, the Mask Shared Secret checkbox is selected, which causes the shared secret to be displayed as black circles in the Shared Secret and Confirm Shared Secret fields. To see the shared secret in both fields, deselect the checkbox.
10. Optionally, specify a Local IKE ID and Peer IKE ID for this Policy. By default, the IP Address (ID_IPv4_ADDR) is used for Main Mode negotiations, and the firewall Identifier (ID_USER_FQDN) is used for Aggressive Mode.
You can select from the following IDs:
– IPv4 Address
– Domain Name
– E-mail Address
– Firewall Identifier
– Key Identifier
Then, enter the address, name, or ID in the field after the drop-down menu.
11. Click the Network tab.
Note If you selected Tunnel Interface for Policy Type on the General tab, the Network tab does not display. Go to 14..
12. Under Local Networks, select one of these
• If a specific local network can access the VPN tunnel, select a local network from the Choose local network from list drop-down menu.
• If traffic can originate from any local network, select Any Address. Use this option if a peer has Use this VPN tunnel as default route for all Internet traffic selected. Auto-added rules will be created between Trusted Zones and the VPN Zone.
Note DHCP over VPN is not supported with IKEv2.
13. Under Destination Networks, select one of these:
• If traffic from any local user cannot leave the firewall unless it is encrypted, select Use this VPN Tunnel as default route for all Internet traffic.
Note You can only configure one SA to use this setting.
• Alternatively, select Choose Destination network from list, and select the address object or group.
15. Under IKE (Phase 1) Proposal, select one of these from the Exchange menu:
• Main Mode
• Aggressive Mode – Generally used when WAN addressing is dynamically assigned.
• IKEv2 Mode – Causes all negotiation to happen via IKE v2 protocols, rather than using IKE Phase 1 and Phase 2.
Note If you select IKE v2 Mode, both ends of the VPN tunnel must use IKE v2.
If IKE v2 is selected, these options are dimmed: DH Group, Encryption, and Authentication.
16. Under IKE (Phase 1) Proposal, the default values for DH Group, Encryption, Authentication, and Life Time are acceptable for most VPN configurations.
Note Be sure the Phase 1 values on the opposite side of the tunnel are configured to match.
17. If you selected Main Mode or Aggressive Mode, for enhanced authentication security you can also choose AES-128, AES-192, or AES-256 from the Authentication menu instead of 3DES.
18. in the IPsec (Phase 2) Proposal section, the default values for Protocol, Encryption, Authentication, Enable Perfect Forward Secrecy, and Life Time (seconds) are acceptable for most VPN SA configurations.
Note Be sure the Phase 2 values on the opposite side of the tunnel are configured to match.
19. Click the Advanced tab and select any of the following optional settings you want to apply to your VPN policy. The options change depending on whether in the Proposals tab you selected
• Main Mode or Aggressive Mode
• IKEv2 Mode
Main Mode or Aggressive Mode Options
• Select Enable Keep Alive to use heartbeat messages between peers on this VPN tunnel. If one end of the tunnel fails, using Keepalives will allow for the automatic renegotiation of the tunnel once both sides become available again without having to wait for the proposed Life Time to expire.
Note The Keep Alive option will be disabled when the VPN policy is configured as a central gateway for DHCP over VPN or with a primary gateway name or address 0.0.0.0.
• The Suppress automatic Access Rules creation for VPN Policy setting is not enabled by default to allow the VPN traffic to traverse the appropriate zones.
• Select Disable IPsec Anti-Replay to disable anti-replay, which is a form of partial sequence integrity that detects the arrival of duplicate IP datagrams (within a constrained window).
• To require XAUTH authentication by users prior to allowing traffic to traverse this tunnel, select Require authentication of VPN client by XAUTH and then select a User group to specify allowed users from the now displayed User group for XAUTH drop-down menu.
• Select Enable Windows Networking (NetBIOS) Broadcast to allow access to remote network resources by browsing the Windows® Network Neighborhood.
• Select Enable Multicast to allow IP multicasting traffic, such as streaming audio (including VoIP) and video applications, to pass through the VPN tunnel.
• Select Permit Acceleration to enable redirection of traffic matching this policy to the WAN Acceleration (WXA) appliance.
• Select Apply NAT Policies if you want the firewall to translate the Local, Remote or both networks communicating via this VPN tunnel. To perform Network Address Translation on the Local Network, select or create an Address Object in the Translated Local Network menu. To translate the Remote Network, select or create an Address Object in the now displayed Translated Remote Network drop-down menu.
Note Generally, if NAT is required on a tunnel, either Local or Remote should be translated, but not both. Apply NAT Policies is particularly useful in cases where both sides of a tunnel use either the same or overlapping subnets.
• To manage the local SonicWALL through the VPN tunnel, select HTTPS from Management via this SA.
• Select HTTP, HTTPS, or both in the User login via this SA to allow users to login using the SA.
• If you wish to use a router on the LAN for traffic entering this tunnel destined for an unknown subnet, for example, if you configured the other side to Use this VPN Tunnel as default route for all Internet traffic, you should enter the IP address of your router into the Default LAN Gateway (optional) field.
• Select an interface or zone from the VPN Policy bound to drop-down menu. A Zone WAN is the preferred selection if you are using WAN Load Balancing and you wish to allow the VPN to use either WAN interface.
IKEv2 Mode Options
When IKE2 Mode is selected on the Proposals tab, the Advanced tab has two sections:
• Advanced Settings
The Advanced Settings are the same as for Main Mode or Aggressive Mode Options with these exceptions:
– The Enable Keep Alive option is dimmed.
– The Require authentication of VPN clients by XAUTH option is not displayed.
• IKEv2 Settings
– The Do not send trigger packet during IKE SA negotiation checkbox is not selected by default and should be selected only when required for interoperability if the peer cannot handle trigger packets.
The term Trigger Packet refers to the use of initial Traffic Selector payloads populated with the IP addresses from the packet that caused SA negotiation to begin. It is recommended practice to include Trigger Packets to assist the IKEv2 Responder in selecting the correct protected IP address ranges from its Security Policy Database. Not all implementations support this feature, so it may be appropriate to disable the inclusion of Trigger Packets to some IKE peers.
– Select one or both of the following two options for the IKEv2 VPN policy (Suite B Crytography support):
: •: Accept Hash & URL Certificate Type
: •: Send Hash & URL Certificate Type
Select these options if your devices can send and process hash and certificate URLs instead of the certificates themselves. Using these options reduces the size of the messages exchanged.
When the Accept Hash & URL Certificate Type option is selected, the firewall sends an HTTP_CERT_LOOKUP_SUPPORTED message to the peer device. If the peer device replies by sending a “Hash and URL of X.509c” certificate, the firewall can authenticate and establish a tunnel between the two devices.
When the Send Hash & URL Certificate Type option is selected, the firewall, on receiving an HTTP_CERT_LOOKUP_SUPPORTED message, sends a "Hash and URL of X.509c” certificate to the requestor.
In a VPN, two peer firewalls (FW1 and FW2) negotiate a tunnel. From the perspective of FW1, FW2 is the remote gateway and vice versa.
20. Click OK.
Configuring a VPN Policy using Manual Key
To manually configure a VPN policy between two SonicWALL appliances using Manual Key, follow the steps below:
Configuring the Local Dell SonicWALL Network Security Appliance
1. Click Add on the VPN > Settings page. The VPN Policy window is displayed.
2. In the General tab of the VPN Policy window, select Manual Key from the Authentication Method drop-down menu. The VPN Policy window displays only the Manual Key options.
3. Enter a name for the policy in the Name field.
4. Enter the host name or IP address of the remote connection in the IPsec Gateway Name or Address field.
5. Click the Network tab.
6. Under Local Networks, select one of these
• If a specific local network can access the VPN tunnel, select a local network from the Choose local network from list drop-down menu.
• If traffic can originate from any local network, select Any Address. Use this option if a peer has Use this VPN tunnel as default route for all Internet traffic selected. Auto-added rules will be created between Trusted Zones and the VPN Zone.
7. Under Destination Networks, select one of these:
• If traffic from any local user cannot leave the firewall unless it is encrypted, select Use this VPN Tunnel as default route for all Internet traffic.
Note You can only configure one SA to use this setting.
• Alternatively, select Choose Destination network from list, and select the address object or group.
8. Click on the Proposals tab.
9. Define an Incoming SPI and an Outgoing SPI. The SPIs are hexadecimal (0123456789abcedf) and can range from 3 to 8 characters in length.
CAUTION Each Security Association must have unique SPIs; no two Security Associations can share the same SPIs. However, each Security Association Incoming SPI can be the same as the Outgoing SPI.
10. The default values for Protocol, Encryption, and Authentication are acceptable for most VPN SA configurations.
Note The values for Protocol, Encryption, and Authentication must match the values on the remote firewall.
11. Enter a 48-character hexadecimal encryption key in the Encryption Key field or use the default value. This encryption key is used to configure the remote SonicWALL encryption key, therefore, write it down to use when configuring the firewall.
12. Enter a 40-character hexadecimal authentication key in the Authentication Key field or use the default value. Write down the key to use while configuring the firewall settings.
Tip Valid hexadecimal characters include 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, a, b, c, d, e, and f. 1234567890abcdef is an example of a valid DES or ARCFour encryption key. If you enter an incorrect encryption key, an error message is displayed at the bottom of the browser window.
13. Click the Advanced tab and select any of the following optional settings you want to apply to your VPN policy.
• The Suppress automatic Access Rules creation for VPN Policy setting is not enabled by default to allow the VPN traffic to traverse the appropriate zones.
• Select Enable Windows Networking (NetBIOS) broadcast to allow access to remote network resources by browsing the Windows® Network Neighborhood.
• Select Permit Acceleration to enable redirection of traffic matching this policy to the WAN Acceleration (WXA) appliance.
• Select Apply NAT Policies if you want the firewall to translate the Local, Remote or both networks communicating via this VPN tunnel. Two drop-down menus display:
– To perform Network Address Translation on the Local Network, select or create an Address Object in the Translated Local Network menu.
– To translate the Remote Network, select or create an Address Object in the Translated Remote Network drop-down menu.
Note Generally, if NAT is required on a tunnel, either Local or Remote should be translated, but not both. Apply NAT Policies is particularly useful in cases where both sides of a tunnel use either the same or overlapping subnets.
Tip Informational videos with interface configuration examples are available online. For example, see How to Configure NAT over VPN in a Site to Site VPN with Overlapping Networks.
Additional videos are available at: https://support.software.dell.com/videos-product-select.
• To manage the local SonicWALL through the VPN tunnel, select HTTPS, SSH, SNMP, or any combination of these three from Management via this SA.
• Select HTTP, HTTPS, or both in the User login via this SA to allow users to login using the SA.
• If you have an IP address for a gateway, enter it into the Default LAN Gateway (optional) field.
• Select an interface from the VPN Policy bound to drop-down menu.
14. Click OK.
15. Click Accept on the VPN > Settings page to update the VPN Policies.
Configuring the Remote Dell SonicWALL Network Security Appliance
1. Click Add on the VPN > Settings page. The VPN Policy window is displayed.
2. In the General tab, select Manual Key from the Authentication Method drop-down menu.
3. Enter a name for the SA in the Name field.
4. Enter the host name or IP address of the local connection in the IPsec Gateway Name or Address field.
5. Click the Network tab.
6. Under Local Networks, select one of these
• If a specific local network can access the VPN tunnel, select a local network from the Choose local network from list drop-down menu.
• If traffic can originate from any local network, select Any Address. Use this option if a peer has Use this VPN tunnel as default route for all Internet traffic selected. Auto-added rules will be created between Trusted Zones and the VPN Zone.
7. Under Destination Networks, select one of these:
• If traffic from any local user cannot leave the firewall unless it is encrypted, select Use this VPN Tunnel as default route for all Internet traffic.
Note You can only configure one SA to use this setting.
• Alternatively, select Choose Destination network from list, and select the address object or group.
8. Click the Proposals tab.
9. Define an Incoming SPI and an Outgoing SPI. The SPIs are hexadecimal (0123456789abcedf) and can range from 3 to 8 characters in length.
CAUTION Each Security Association must have unique SPIs; no two Security Associations can share the same SPIs. However, each Security Association Incoming SPI can be the same as the Outgoing SPI.
10. The default values for Protocol, Encryption, and Authentication are acceptable for most VPN SA configurations.
Note The values for Protocol, Encryption, and Authentication must match the values on the remote firewall.
11. Enter a 48-character hexadecimal encryption key in the Encryption Key field or use the default value. This encryption key is used to configure the remote SonicWALL encryption key, therefore, write it down to use when configuring the remote SonicWALL.
12. Enter a 40-character hexadecimal authentication key in the Authentication Key field or use the default value. Write down the key to use while configuring the remote SonicWALL settings.
Tip Valid hexadecimal characters include 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, a, b, c, d, e, and f. 1234567890abcdef is an example of a valid DES or ARCFour encryption key. If you enter an incorrect encryption key, an error message is displayed at the bottom of the browser window.
13. Click the Advanced tab and select any of the following optional settings you want to apply to your VPN policy:
• The Suppress automatic Access Rules creation for VPN Policy setting is not enabled by default to allow the VPN traffic to traverse the appropriate zones.
• Select Enable Windows Networking (NetBIOS) broadcast to allow access to remote network resources by browsing the Windows® Network Neighborhood.
• Select Permit Acceleration to enable redirection of traffic matching this policy to the WAN Acceleration (WXA) appliance.
• Select Apply NAT Policies if you want the firewall to translate the Local, Remote or both networks communicating via this VPN tunnel. Two drop-down menus display:
– To perform Network Address Translation on the Local Network, select or create an Address Object in the Translated Local Network menu.
– To translate the Remote Network, select or create an Address Object in the Translated Remote Network drop-down menu.
Note Generally, if NAT is required on a tunnel, either Local or Remote should be translated, but not both. Apply NAT Policies is particularly useful in cases where both sides of a tunnel use either the same or overlapping subnets.
• To manage the remote SonicWALL through the VPN tunnel, select HTTP, SSH, SNMP, or any combination of these three from Management via this SA.
• Select HTTP, HTTPS, or both in the User login via this SA to allow users to login using the SA.
• If you have an IP address for a gateway, enter it into the Default LAN Gateway (optional) field.
• Select an interface from the VPN Policy bound to menu.
14. Click OK.
15. Click Accept on the VPN > Settings page to update the VPN Policies.
Tip Since Window Networking (NetBIOS) has been enabled, users can view remote computers in their Windows Network Neighborhood. Users can also access resources on the remote LAN by entering servers’ or workstations’ remote IP addresses.
Configuring a VPN Policy with IKE using a Third Party Certificate
Note You must have a valid certificate from a third party Certificate Authority installed on your SonicWALL before you can configure your VPN policy with IKE using a third party certificate.
To create a VPN SA using IKE and third party certificates, follow these steps:
1. In the VPN > Settings page, click Add. The VPN Policy window is displayed.
2. In the Authentication Method list in the General tab, select IKE using 3rd Party Certificates.The VPN Policy window displays the third-party certificate options in the IKE Authentication section.
3. Type a Name for the Security Association in the Name field.
4. Type the IP address or Fully Qualified Domain Name (FQDN) of the primary remote SonicWALL in the IPsec Primary Gateway Name or Address field.
5. If you have a secondary remote SonicWALL, enter the IP address or Fully Qualified Domain Name (FQDN) in the IPsec Secondary Gateway Name or Address field.
6. Under IKE Authentication, select a third-party certificate from the Local Certificate list. You must have imported local certificates before selecting this option.
7. Select one of the following Peer ID types from the Peer IKE ID Type menu:
• Email ID (UserFQDN) and Domain Name (FQDN) - The Email ID (UserFQDN) and Domain Name (FQDN) types are based on the certificate's Subject Alternative Name field, which is not contained in all certificates by default. If the certificate contains a Subject Alternative Name, that value must be used. For site-to-site VPNs, wild card characters (such as * for more than one character or ? for a single character) cannot be used.
The full value of the Email ID or Domain Name must be entered. This is because site-to-site VPNs are expected to connect to a single peer, as opposed to Group VPNs, which expect to connect to multiple peers.
Note To find the certificate details (Subject Alternative Name, Distinguished Name, etc.), navigate to the System > Certificates page and click on the ![]() Export button for the certificate.
Export button for the certificate.
• Distinguished Name (DN) - Based on the certificates Subject Distinguished Name field, which is contained in all certificates by default. As with the Email ID and Domain Name above, the entire Distinguished Name field must be entered for site-to-site VPNs. Wild card characters are not supported.
The format of any Subject Distinguished Name is determined by the issuing Certificate Authority. Common fields are Country (C=), Organization (O=), Organizational Unit (OU=), Common Name (CN=), Locality (L=), and vary with the issuing Certificate Authority. The actual Subject Distinguished Name field in an X.509 Certificate is a binary object which must be converted to a string for matching purposes. The fields are separated by the forward slash character, for example: /C=US/O=SonicWALL, Inc./OU=TechPubs/CN=Joe Pub
• IP Address (IPV4) - Based on the IPv4 IP address.
8. Type an ID string in the Peer IKE ID field.
9. Click on the Network tab.
10. Under Local Networks, select one of these
• If a specific local network can access the VPN tunnel, select a local network from the Choose local network from list drop-down menu.
• If traffic can originate from any local network, select Any Address. Use this option if a peer has Use this VPN tunnel as default route for all Internet traffic selected. Auto-added rules will be created between Trusted Zones and the VPN Zone.
11. Under Destination Networks, select one of these:
• If traffic from any local user cannot leave the firewall unless it is encrypted, select Use this VPN Tunnel as default route for all Internet traffic.
Note You can only configure one SA to use this setting.
• Alternatively, select Choose Destination network from list, and select the address object or group.
12. Click the Proposals tab.
13. In the IKE (Phase 1) Proposal section, select the following settings:
• Select Main Mode or Aggressive Mode from the Exchange menu.
• Select the desired DH Group from the DH Group menu:
– Group 1, Group 2, Group 5, or Group 14
– 256-Bit Random ECP Group, 384-Bit Random ECP Group, 521-Bit Random ECP Group, 192-Bit Random ECP Group, or 224-Bit Random ECP Group
• Select 3DES, AES-128, AES-192, or AES-256 from the Encryption menu.
• Select the desired authentication method from the Authentication menu.
• Enter a value in the Life Time (seconds) field. The default setting of 28800 forces the tunnel to renegotiate and exchange keys every 8 hours.
14. In the IPsec (Phase 2) Proposal section, select the following settings:
• Select the desired protocol from the Protocol menu.
• Select 3DES, AES-128, AES-192, or AES-256 from the Encryption menu.
• Select the desired authentication method from the Authentication menu.
• Select Enable Perfect Forward Secrecy if you want an additional Diffie-Hellman key exchange as an added layer of security. Select Group 2 from the DH Group menu.
• Enter a value in the Life Time (seconds) field. The default setting of 28800 forces the tunnel to renegotiate and exchange keys every 8 hours.
15. Click the Advanced tab. Select any optional configuration options you want to apply to your VPN policy:
• Select Enable Keep Alive to use heartbeat messages between peers on this VPN tunnel. If one end of the tunnel fails, using Keepalives will allow for the automatic renegotiation of the tunnel once both sides become available again without having to wait for the proposed Life Time to expire.
• The Suppress automatic Access Rules creation for VPN Policy setting is not enabled by default to allow the VPN traffic to traverse the appropriate zones.
• Select Disable IPsec Anti-Replay to disable anti-replay, which is a form of partial sequence integrity that detects the arrival of duplicate IP datagrams (within a constrained window).
• To require XAUTH authentication by users prior to allowing traffic to traverse this tunnel, select Require authentication of VPN client by XAUTH, and select a User group to specify allowed users from the User group for XAUTH.
• Select Enable Windows Networking (NetBIOS) Broadcast to allow access to remote network resources by browsing the Windows® Network Neighborhood.
• Select Enable Multicast to allow multicast traffic through the VPN tunnel.
• Select Permit Acceleration to enable redirection of traffic matching this policy to the WAN Acceleration (WXA) appliance
• Select Apply NAT Policies if you want the firewall to translate the Local, Remote or both networks communicating via this VPN tunnel. To perform Network Address Translation on the Local Network, select or create an Address Object in the Translated Local Network menu. To translate the Remote Network, select or create an Address Object in the Translated Remote Network menu. Generally, if NAT is required on a tunnel, either Local or Remote should be translated, but not both. Apply NAT Policies is particularly useful in cases where both sides of a tunnel use either the same or overlapping subnets.
• Select Enable OCSP Checking to check VPN certificate status and specify the URL where to check certificate status. See Using OCSP with Dell SonicWALL Network Security Appliances.
• To manage the remote SonicWALL through the VPN tunnel, select HTTP, HTTPS, or both from Management via this SA. Select HTTP, SSH, HTTPS, or any combination of the three in the User login via this SA to allow users to login using the SA.
• If you wish to use a router on the LAN for traffic entering this tunnel destined for an unknown subnet, for example, if you configured the other side to Use this VPN Tunnel as default route for all Internet traffic, you should enter the IP address of your router into the Default LAN Gateway (optional) field.
• Select an interface or zone from the VPN Policy bound to menu. A zone is the preferred selection if you are using WAN Load Balancing and you wish to allow the VPN to use either WAN interface.
• Under IKEv2 Settings (visible only if you selected IKEv2 for Exchange on the Proposals tab), The Do not send trigger packet during IKE SA negotiation checkbox is cleared by default and should only be selected when required for interoperability.
The term Trigger Packet refers to the use of initial Traffic Selector payloads populated with the IP addresses from the packet that caused SA negotiation to begin. It is recommended practice to include Trigger Packets to assist the IKEv2 Responder in selecting the correct protected IP address ranges from its Security Policy Database. Not all implementations support this feature, so it may be appropriate to disable the inclusion of Trigger Packets to some IKE peers.
• Select one or both of the following two options for the IKEv2 VPN policy:
– Accept Hash & URL Certificate Type
– Send Hash & URL Certificate Type
Select these options if your devices can send and process hash and certificate URLs instead of the certificates themselves. Using these options reduces the size of the messages exchanged.
When the Accept Hash & URL Certificate Type option is selected, the firewall sends an HTTP_CERT_LOOKUP_SUPPORTED message to the peer device. If the peer device replies by sending a “Hash and URL of X.509c” certificate, the firewall can authenticate and establish a tunnel between the two devices.
When the Send Hash & URL Certificate Type option is selected, the firewall, on receiving an HTTP_CERT_LOOKUP_SUPPORTED message, sends a "Hash and URL of X.509c” certificate to the requestor.
In a VPN, two peer firewalls (FW1 and FW2) negotiate a tunnel. From the perspective of FW1, FW2 is the remote gateway and vice versa.
16. Click OK.
Configuring VPN Failover to a Static Route
Optionally, you can configure a static route to be used as a secondary route in case the VPN tunnel goes down. The Allow VPN path to take precedence option allows you to create a secondary route for a VPN tunnel. By default, static routes have a metric of one and take precedence over VPN traffic. The Allow VPN path to take precedence option gives precedence over the route to VPN traffic to the same destination address object. This results in the following behavior:
• When a VPN tunnel is active: static routes matching the destination address object of the VPN tunnel are automatically disabled if the Allow VPN path to take precedence option is enabled. All traffic is routed over the VPN tunnel to the destination address object.
• When a VPN tunnel goes down: static routes matching the destination address object of the VPN tunnel are automatically enabled. All traffic to the destination address object is routed over the static routes.
To configure a static route as a VPN failover, complete the following steps:
1. Navigate to the Network > Routing page.
2. Scroll to the bottom of the page and click on the Add button. The Add Route Policy window is displayed.
3. Select the appropriate Source, Destination, Service, Gateway, and Interface.
4. Ensure Metric is 1.
5. Enable the Allow VPN path to take precedence checkbox.
6. Click OK.
For more information on configuring static routes and Policy Based Routing, see Network > Routing.
A policy-based approach forces the VPN policy configuration to include the network topology configuration. This makes it difficult for the network administrator to configure and maintain the VPN policy with a constantly changing network topology.
With the Route Based VPN approach, network topology configuration is removed from the VPN policy configuration. The VPN policy configuration creates a Tunnel Interface between two end points. Static or Dynamic routes can then be added to the Tunnel Interface. The Route Based VPN approach moves network configuration from the VPN policy configuration to Static or Dynamic Route configuration.
Not only does Route Based VPN make configuring and maintaining the VPN policy easier, a major advantage of the Route Based VPN feature is that it provides flexibility on how traffic is routed. With this feature, users can now define multiple paths for overlapping networks over a clear or redundant VPN.
Topics:
• Route Entries for Different Network Segments
Route Based VPN configuration is a two step process. The first step involves creating a Tunnel Interface. The crypto suites used to secure the traffic between two end-points are defined in the Tunnel Interface. The second step involves creating a static or dynamic route using Tunnel Interface.
The Tunnel Interface is created when a Policy of type “Tunnel Interface” is added for the remote gateway. The Tunnel Interface must be bound to a physical interface and the IP address of that physical interface is used as the source address of the tunneled packet.
Topics:
• Creating a Static Route for Tunnel Interface
The following procedures explain how to add a Tunnel Interface:
1. Navigate to VPN>Settings>VPN Policies.
2. Click the Add button. This will open the VPN Policy dialog box.
3. On the General tab, select the policy type as Tunnel Interface. The Network tab is removed.
4. Next, click the Proposals tab.
5. Configure the IKE (Phase 1) Proposal and IPSec (Phase 2) Proposal options for the tunnel negotiation.
6. Click the Advanced tab to configure the advanced properties for the Tunnel Interface. By default, Enable Keep Alive is enabled. This is to establish the tunnel with remote gateway proactively.
7. The following other advanced options can be configured:
• Disable IPsec Anti-Replay - Disables anti-replay, which is a form of partial sequence integrity that detects the arrival of duplicate IP datagrams (within a constrained window).
• Allow Advanced Routing - Adds this Tunnel Interface to the list of interfaces in the Advanced Routing table on the Network > Routing page.
Making this an optional setting avoids adding all Tunnel Interfaces to the Advanced Routing table, which helps streamline the routing configuration. See Configuring Advanced Routing for Tunnel Interfaces for information on configuring RIP or OSPF advanced routing for the Tunnel Interface.
• Enable Transport Mode - Forces the IPsec negotiation to use Transport mode instead of Tunnel Mode. This has been introduced for compatibility with Nortel. When this option is enabled on the local firewall, it MUST be enabled on the remote firewall as well for the negotiation to succeed.
• Enable Windows Networking (NetBIOS) Broadcast - Allows access to remote network resources by browsing the Windows® Network Neighborhood.
• Enable Multicast - Allows multicast traffic through the VPN tunnel.
• Permit Acceleration - Enables redirection of traffic matching this policy to the WAN Acceleration (WXA) appliance
• Management via this SA - Allows remote users to log in to manage the firewall through the VPN tunnel. Select one or more: HTTPS, SSH, SNMP.
• User login via this SA - Allows users to login using the SA.
• VPN Policy bound to - Sets the interface the Tunnel Interface is bound to. This is Interface X1 by default.
8. If IKEv2 Mode was selected on the Proposals tab, configure the IKEv2 Settings:
• The Do not send trigger packet during IKE SA negotiation checkbox is not selected by default and should be selected only when required for interoperability if the peer cannot handle trigger packets.
The term Trigger Packet refers to the use of initial Traffic Selector payloads populated with the IP addresses from the packet that caused SA negotiation to begin. It is recommended practice to include Trigger Packets to assist the IKEv2 Responder in selecting the correct protected IP address ranges from its Security Policy Database. Not all implementations support this feature, so it may be appropriate to disable the inclusion of Trigger Packets to some IKE peers.
• Select one or both of the following two options for the IKEv2 VPN policy:
– Accept Hash & URL Certificate Type – The firewall sends an HTTP_CERT_LOOKUP_SUPPORTED message to the peer device. If the peer device replies by sending a “Hash and URL of X.509c” certificate, the firewall can authenticate and establish a tunnel between the two devices.
– Send Hash & URL Certificate Type – The firewall, on receiving an HTTP_CERT_LOOKUP_SUPPORTED message, sends a "Hash and URL of X.509c” certificate to the requestor.
Select these options if your devices can send and process hash and certificate URLs instead of the certificates themselves. Using these options reduces the size of the messages exchanged.
In a VPN, two peer firewalls (FW1 and FW2) negotiate a tunnel. From the perspective of FW1, FW2 is the remote gateway and vice versa.
9. Click OK.
Creating a Static Route for Tunnel Interface
After you have successfully added a Tunnel Interface, you may then create a Static Route. Follow the procedures to create a Static Route for a Tunnel Interface:
Navigate to Network>Routing>Route Policies. Click the Add button. A dialogue window appears for adding Static Route. Note that the “Interface” drop-down menu lists all available tunnel interfaces.
Note If the “Auto-add Access Rule” option is selected, firewall rules are automatically added and traffic is allowed between the configured networks using tunnel interface.
Route Entries for Different Network Segments
After a tunnel interface is created, multiple route entries can be configured to use the same tunnel interface for different networks. This provides a mechanism to modify the network topology without making any changes to the tunnel interface.
Redundant Static Routes for a Network
After more than one tunnel interface is configured, you can add multiple overlapping static routes; each static route uses a different tunnel interface to route the traffic. This provides routing redundancy for the traffic to reach the destination.
The drop tunnel interface is a pre-configured tunnel interface. This interface provides added security for traffic. An example of this would be if a static route bind interface is deemed the drop tunnel interface, then all the traffic for that route is dropped and not forwarded in clear. If a static route bind to tunnel interface is defined for traffic (source/destination/service), and it is desired that traffic should not be forwarded in the clear if the tunnel interface is down, it is recommended to configure a static route bind to drop tunnel interface for the same network traffic. As a result, if the tunnel interface is down, traffic will be dropped due to the drop tunnel interface static route.
Creating a Static Route for Drop Tunnel Interface
To add a static route for drop tunnel interface:
1. Navigate to Network > Routing > Route Policies.
2. Click the Add button. The Add Route Policy window displays.
3. Similar to configuring a static route for a tunnel interface, configure the values for Source, Destination, and Service options.
4. Under Interface, select Drop_tunnelIf.
5. Click OK.
Once added, the route is enabled and displayed in the Route Polices.
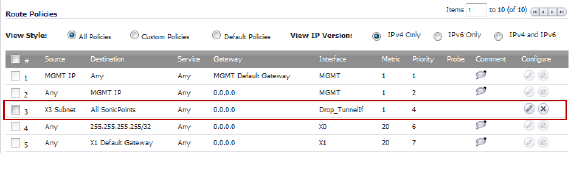
VPN Auto-Added Access Rule Control
When adding VPN Policies, SonicOS auto-creates non-editable Access Rules to allow the traffic to traverse the appropriate zones. Consider the following VPN Policy, where the Local Network is set to Firewalled Subnets (in this case comprising the LAN and DMZ) and the Destination Network is set to Subnet 192.168.169.0.
While this is generally a tremendous convenience, there are some instances where is might be preferable to suppress the auto-creation of Access Rules in support of a VPN Policy. One such instance would be the case of a large hub-and-spoke VPN deployment where all the spoke site are addresses using address spaces that can easily be supernetted. For example, assume we wanted to provide access to/from the LAN and DMZ at the hub site to one subnet at each of 2,000 remote sites, addressed as follows:
remoteSubnet0=Network 10.0.0.0/24 (mask 255.255.255.0, range 10.0.0.0-10.0.0.255)
remoteSubnet1=Network 10.0.1.0/24 (mask 255.255.255.0, range 10.0.1.0-10.0.1.255)
remoteSubnet2=Network 10.0.2.0/24 (mask 255.255.255.0, range 10.0.2.0-10.0.2.255)
remoteSubnet2000=10.7.207.0/24 (mask 255.255.255.0, range 10.7.207.0-10.7.207.255)
Creating VPN Policies for each of these remote sites would result in the requisite 2,000 VPN Policies, but would also create 8,000 Access Rules (LAN -> VPN, DMZ -> VPN, VPN -> LAN, and VPN -> DMZ for each site). However, all of these Access Rules could easily be handled with just 4 Access Rules to a supernetted or address range representation of the remote sites (More specific allow or deny Access Rules could be added as needed):
remoteSubnetAll=Network 10.0.0.0/13 (mask 255.248.0.0, range 10.0.0.0-10.7.255.255) or
remoteRangeAll=Range 10.0.0.0-10.7.207.255
To enable this level of aggregation, the Advanced tab of the VPN Policy window page offers the option to Auto-Add Access Rules for VPN Policy setting. By default, the checkbox is selected, meaning the accompanying Access Rules will be automatically created, as they've always been. By deselecting the checkbox upon creating the VPN Policy, the administrator will have the ability and need to create custom Access Rules for VPN traffic.